Zero Trust Security for
Financial Infrastructure
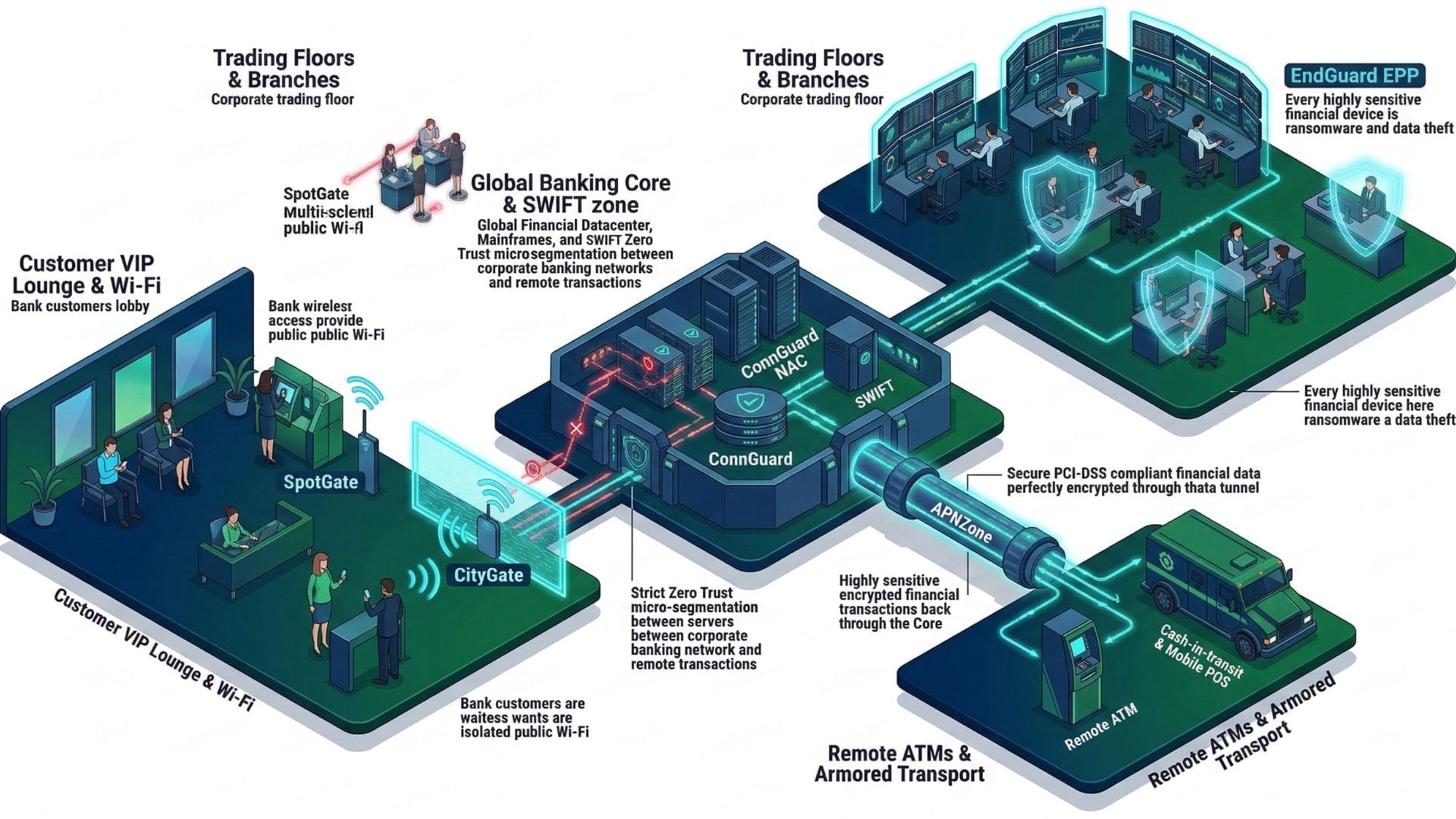
Financial institutions operate complex infrastructures spanning
branch networks, ATM systems, trading platforms, payment networks,
and cloud workloads.
S3M Security delivers identity-driven Zero Trust architecture
designed to secure financial networks, protect payment systems,
and enforce device trust across distributed banking environments.
The Expanding Cyber Risk in Retail Banking Infrastructure
Retail banking has transformed into a highly distributed digital ecosystem.
Branches, ATM networks, mobile applications, payment gateways, and cloud banking platforms now operate simultaneously across thousands of endpoints.
While this transformation enables real-time financial services and seamless customer experiences, it also dramatically expands the attack surface.
Modern retail banking networks must protect infrastructure that extends far beyond traditional data centers — often across public networks, third-party integrations, and customer-facing channels.
Without identity-driven security controls, these distributed environments create structural exposure across critical financial systems.
ATM Network Exposure
ATM fleets operate across geographically distributed networks often connected through carrier infrastructure. Without strong identity verification and encrypted connectivity, ATM communication channels become attractive targets for fraud, skimming operations, and transaction manipulation.
Distributed Branch Infrastructure
Retail banks operate hundreds or thousands of branch locations connected through WAN environments. Legacy network models struggle to maintain consistent access control and visibility across these distributed operational systems.
Mobile Banking Attack Surface
Mobile banking applications introduce millions of external access sessions into banking infrastructure. Authentication abuse, session hijacking, and API exploitation represent growing risks when identity validation is not continuously enforced.
Third-Party Fintech Integrations
Open banking ecosystems require integration with payment processors, fintech platforms, and external financial services. These integrations expand trust boundaries and introduce new attack vectors into banking environments.
Limited Identity Visibility
Many financial institutions still lack real-time visibility into device identity, endpoint posture, and user context across their network infrastructure, creating blind spots that attackers can exploit.
Regulatory Compliance Pressure
Retail banking infrastructure must operate under strict regulatory frameworks including PCI DSS, PSD2, GDPR, and national financial security regulations, requiring full visibility and traceability of network access.
Retail banking cybersecurity can no longer rely on perimeter defenses.
Security must be enforced continuously across identities, devices, and financial infrastructure.
Perimeter-Based Security Cannot Protect Modern Financial Networks
Modern financial infrastructure no longer operates within a clearly defined perimeter.
Retail banking networks extend across branch offices, ATM networks, mobile banking platforms, cloud services, and third-party financial ecosystems.
Traditional network security models assume that internal networks are trustworthy and external networks are hostile.
In modern financial environments this assumption is no longer valid.
Attackers frequently enter through compromised credentials, infected endpoints, or third-party integrations — bypassing perimeter defenses entirely.

Flat Network Architecture
Traditional banking networks often rely on flat internal architectures where systems communicate freely once access is granted. When attackers compromise a single endpoint, they can move laterally across financial infrastructure without encountering meaningful barriers.
Credential-Based Access
Many financial systems still rely heavily on static credentials for authentication. When these credentials are stolen through phishing campaigns or password reuse, attackers can gain persistent access to sensitive banking infrastructure.
Hybrid Cloud Complexity
Many financial systems still rely heavily on static credentials for authentication. When these credentials are stolen through phishing campaigns or password reuse, attackers can gain persistent access to sensitive banking infrastructure.
Lateral Movement Risk
Once attackers gain initial access to banking networks they can often move laterally between systems due to insufficient segmentation, allowing deeper compromise of financial infrastructure.
Modern financial cybersecurity can no longer depend on perimeter-based defenses.
Financial institutions must continuously verify identities, validate device trust, and enforce network segmentation across users, systems, and applications.
Only an identity-driven Zero Trust architecture can provide the visibility and control required to secure modern banking infrastructure.
Identity-Driven Zero Trust Architecture for Financial Networks
Financial institutions operate under strict regulatory requirements while managing highly distributed infrastructure.
Security architecture must therefore enforce identity-driven access control, protect financial systems across distributed networks, and maintain continuous visibility required for regulatory compliance.
S3M Security enables financial organizations to secure banking infrastructure while aligning with global financial security standards.
Compliance Exposure Points
- Payment processing infrastructure must protect cardholder data environments and prevent unauthorized transaction access.
- Branch networks and ATM systems require strong identity verification and encrypted communication channels.
- Hybrid banking infrastructure introduces complex access patterns across on-premise and cloud systems.
- Internal user access to financial systems must be continuously verified to prevent credential misuse.
- Distributed banking infrastructure must prevent lateral movement between financial services environments.
Regulatory Framework Examples
- PCI DSS compliance for payment infrastructure security and cardholder data protection.
- PSD2 security requirements for strong customer authentication and secure payment services.
- GDPR obligations requiring strict protection of personal financial data.
- SOX controls ensuring financial system integrity and secure access governance.
- Distributed banking infrastructure must prevent lateral movement between financial services environments.
- SWIFT security framework requirements for secure financial messaging infrastructure.
Financial cybersecurity must simultaneously protect infrastructure and demonstrate regulatory compliance.
Identity-driven Zero Trust architecture enables financial institutions to enforce strong access control, maintain continuous visibility, and protect critical financial systems across distributed banking environments.
Zero Trust Financial Network Security Architecture
S3M Security enforces identity-driven security across financial infrastructure, protecting users, devices, and applications across distributed banking networks.
The architecture ensures that every connection is authenticated, every device is validated, and every network interaction is continuously monitored.
Identity Verification Layer
User identity verification ensures that only authenticated financial system users can access sensitive banking applications and infrastructure.
Identity Verification Layer
User identity verification ensures that only authenticated financial system users can access sensitive banking applications and infrastructure.
Device Trust Layer
Network segmentation isolates banking infrastructure, preventing lateral movement across systems even if an endpoint becomes compromised.
This architecture provides financial institutions with continuous visibility, strong identity enforcement, and secure network segmentation required to protect modern banking infrastructure.
Real-World Banking Security Scenarios
Financial institutions operate across complex environments that include branches, ATM fleets, payment systems, and digital banking platforms.
S3M Security protects these environments by enforcing identity-driven access control, device verification, and secure network segmentation across financial infrastructure.
Third-Party Fintech Integration Security
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Payment Processing Infrastructure Security
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
ATM Network Infrastructure Security
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Branch Network Access Governance
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Financial security scenarios demonstrate how identity-driven network security protects banking infrastructure across real operational environments.
Security Scenarios for Modern Financial Infrastructure
Financial institutions operate some of the most complex digital infrastructures in the modern economy. ATM networks, branch offices, mobile banking platforms, payment processing systems, and fintech integrations all require secure and reliable connectivity while maintaining strict regulatory compliance.
Each of these environments introduces different cybersecurity challenges. From unauthorized device access to compromised third-party integrations, financial systems must be protected without disrupting critical services or customer transactions.
S3M Security platforms enable banks and financial service providers to implement identity-driven network security across these operational environments. By combining secure connectivity, device authentication, and intelligent access control, organizations can protect financial infrastructure while maintaining uninterrupted service availability.
ATM Network Security Enforcement
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Branch Network Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Mobile Banking Infrastructure Protection
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Fintech Integration Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Payment Processing Infrastructure Protection
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Interbank Connectivity
Scenario
Threat
Architectural Response
Operational Impact
Security Components
The following operational scenarios demonstrate how financial institutions can secure distributed banking infrastructure, protect payment systems, and maintain trusted connectivity across critical financial services.
Security Platforms Designed for Financial Infrastructure
Financial institutions require security architectures that can operate across highly regulated, distributed, and always-on environments. From ATM networks and branch offices to mobile banking infrastructure and payment processing systems, financial services demand resilient and identity-driven protection.
S3M Security platforms are designed to secure these environments through device identity verification, network segmentation, and secure connectivity between critical financial systems. The architecture enables banks to protect sensitive data, control network access, and ensure trusted communication across distributed infrastructure.
Role Description
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
By combining secure connectivity, device identity, and network access control, S3M Security solutions enable financial institutions to build resilient, scalable, and compliant cybersecurity architectures.
Security Outcomes for Financial Infrastructure Protection
Identity-driven network control enables municipalities to operate complex digital infrastructure securely while maintaining operational agility and citizen accessibility.Financial institutions must secure complex digital ecosystems while maintaining uninterrupted services for customers, partners, and internal operations. ATM networks, mobile banking platforms, payment processing systems, and branch infrastructures all require strong security controls without introducing operational friction.
S3M Security solutions help financial organizations achieve this balance by implementing identity-driven access control, secure connectivity, and intelligent network segmentation. By verifying devices, controlling network access, and protecting communication between critical systems, banks can reduce operational risk while maintaining high service availability.
Unified Security Control Plane
Regulatory Compliance Enablement
Operational Continuity
Scalable Security Governance
By strengthening network visibility, enforcing trusted device access, and protecting critical financial systems, S3M Security enables financial institutions to build resilient cybersecurity architectures that support secure digital banking services and long-term operational stability.
