Retail Zero Trust Network Architecture
Modern retail infrastructure spans hundreds of stores, thousands of POS terminals, mobile workforce devices, and customer connectivity networks.
Traditional perimeter security cannot protect this distributed environment.
S3M Security delivers identity-driven Zero Trust network architecture designed to secure retail infrastructure, protect payment systems, and enforce device-level trust across store networks.
The Expanding Cyber Risk Surface in
Retail Infrastructure
Retail environments now operate as highly distributed digital infrastructures. A single retail organization may manage hundreds of stores, thousands of POS terminals, warehouse networks, customer WiFi services, and cloud-based commerce platforms.
Each additional device, store location, or customer connectivity point expands the potential attack surface. Payment systems, POS infrastructure, and customer identity databases have become high-value targets for cybercriminals seeking financial gain and operational disruption.
Many retailers still rely on security models originally designed for centralized corporate networks. These approaches struggle to provide visibility and control across distributed store environments, leaving critical gaps in device identity, network access, and lateral movement protection.
- Unmanaged POS terminals and store devices connected to internal networks
- Guest WiFi environments that are not properly isolated from operational infrastructure
- Legacy POS systems with limited endpoint protection capabilities
- Third-party vendor access to store and payment systems
- Limited real-time visibility across distributed retail locations
Retail cybersecurity must evolve beyond perimeter-based defenses toward identity-driven network architecture that can enforce trust across every store, device, and connection point.
Why Traditional Retail Security Models Fail
Retail cybersecurity strategies were historically designed around centralized corporate networks. Today, retail infrastructure operates as a distributed environment connecting stores, POS terminals, warehouses, cloud platforms, and mobile workforce devices.
This structural shift exposes the limitations of traditional security approaches built around fixed network boundaries and static access policies.
Firewall-Centric Security
Firewalls were designed to protect fixed network perimeters. In modern retail environments, connectivity originates from distributed store locations, POS devices, cloud services, and mobile workforce endpoints beyond traditional network boundaries.
Static Network Segmentation
Many retailers rely on VLAN-based segmentation to separate POS systems, store operations, and guest WiFi networks. However, static segmentation assumes devices inside a network segment are trustworthy, enabling lateral movement once a device is compromised.
IP-Based Access Policies
Retail infrastructure includes mobile POS devices, tablets, inventory scanners, and IoT sensors that frequently change network locations. Security policies based solely on IP addresses cannot reliably represent device identity or trust level.
Manual Device Onboarding
Retail environments continuously add new devices across stores and warehouses. Manual device onboarding processes introduce configuration inconsistencies and security gaps that are difficult to manage across large retail networks.
Retail cybersecurity can no longer rely on perimeter defenses or static network segmentation. Effective protection requires identity-driven security architecture capable of continuously validating users, devices, and applications across distributed retail infrastructure.
Retail Network Security Architecture
Retail organizations require a security architecture capable of protecting distributed store networks, POS infrastructure, and customer-facing digital services.
Instead of relying on isolated security products, modern retail cybersecurity must operate as an integrated architecture that enforces identity validation, device trust, and network segmentation across every retail location.
Retail Infrastructure Risk Points
POS terminal access and payment processing security
Customer WiFi networks operating alongside operational infrastructure
Third-party vendor access to store systems
Distributed store network connectivity across regions
Device identity validation for POS and retail IoT infrastructure
Retail Compliance & Regulatory Landscape
PCI DSS payment security standards
GDPR customer data protection regulations
ISO 27001 information security management
NIS2 cybersecurity directive for digital infrastructure
Regional financial and payment security regulations
Retail cybersecurity architecture must protect payment systems, store networks, and customer connectivity while maintaining compliance visibility across distributed retail infrastructure.
Zero Trust Retail Security Architecture
Retail infrastructure requires continuous identity validation across users, devices, applications, and store networks. Security must operate as an architectural control layer protecting POS systems, employee devices, customer connectivity, and distributed retail locations.
A Zero Trust architecture ensures that every connection inside the retail environment is verified, segmented, and continuously monitored.
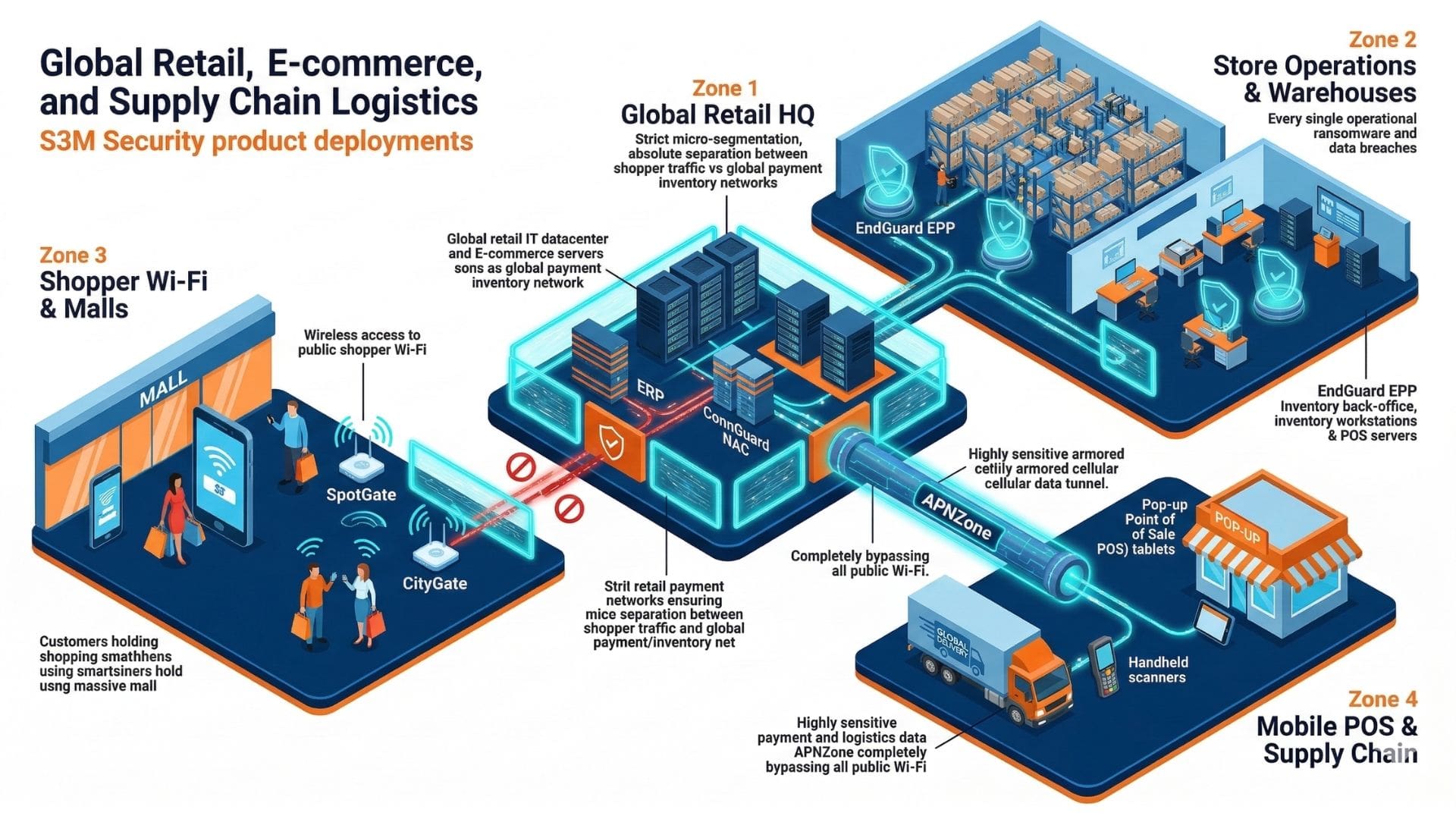
Identity Access Layer
Identity becomes the primary enforcement mechanism across retail infrastructure. Every POS terminal, employee device, vendor system, and store network connection must be authenticated and continuously validated before access is granted.
Access decisions follow identity, not network location.
Endpoint & Device Posture Layer
Retail devices including POS terminals, tablets, inventory scanners, and IoT sensors are evaluated based on compliance state and behavioral indicators. Device posture determines access privileges within the retail network.
Device posture directly influences network segmentation and access privileges.
Guest Connectivity Governance
Customer WiFi networks must remain isolated from operational retail infrastructure. Guest access is authenticated, segmented, and monitored to prevent exposure to store systems or payment networks.
Guest access must remain auditable and structurally separated from operational infrastructure.
Store Network Segmentation
POS infrastructure, store operations networks, and corporate systems are segmented through identity-driven policies that prevent unauthorized lateral movement across retail environments.
Security enforcement extends beyond physical perimeters into mobile and carrier environments.
Distributed Retail Infrastructure Layer
Retail stores, warehouses, and digital commerce platforms connect through encrypted and policy-controlled channels. Security enforcement extends beyond individual stores to protect the entire retail ecosystem.
Retail cybersecurity must operate as a unified architecture across every store location, payment system, and digital commerce platform. Identity-driven security enables retailers to maintain visibility and control across distributed infrastructure without disrupting operational agility.
Architecture in Action
Retail Security Architecture in Real-World
Operational Scenarios
Security architecture proves its value only when it operates under real operational conditions. Retail environments connect stores, POS systems, warehouse infrastructure, cloud commerce platforms, and customer connectivity networks into a single digital ecosystem.
Each of these components introduces new attack surfaces and operational risks. The following scenarios illustrate how identity-driven network security architecture protects retail infrastructure, enforces device trust, and prevents unauthorized access across distributed store environments.
These examples demonstrate how architectural security controls operate in practice across modern retail infrastructure.
Multi-Store Network Connectivity Security
Scenario
Threat
Architectural Response
Operational Impact
Third-Party Vendor Network Access Control
Scenario
Threat
Architectural Response
Operational Impact
Customer WiFi Network Isolation
Scenario
Threat
Architectural Response
Operational Impact
Retail IoT Device Access Governance
Scenario
Threat
Architectural Response
Operational Impact
POS Payment Infrastructure Protection
Scenario
Threat
Architectural Response
Operational Impact
Retail cybersecurity must function dynamically under real operational pressure — not only as a theoretical architectural design. Identity-driven security architecture enables retailers to maintain continuous visibility and control across every store, device, and connection point in the retail ecosystem.
Operational Security
Operational Use Cases Across Retail Infrastructure
Retail environments operate through a complex ecosystem of store networks, POS terminals, connected devices, supply chain systems, and customer connectivity platforms. Security architecture must function across all of these operational layers without disrupting day-to-day retail operations.
Identity-driven network security enables retailers to control device access, isolate customer connectivity, secure vendor interactions, and maintain visibility across distributed store environments.
The following operational use cases illustrate how modern retail security architecture protects payment systems, store infrastructure, and connected retail technologies in real operational conditions.
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Guest Network Isolation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Supply Chain Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Network Visibility
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Retail cybersecurity must operate continuously across every store, device, and connection point in the retail ecosystem. Identity-driven architecture enables retailers to enforce trust, maintain visibility, and protect payment infrastructure while supporting seamless retail operations.
Identity-Driven Security Layers Protecting
Retail Infrastructure
Modern retail infrastructure connects stores, POS systems, employee devices, logistics platforms, and customer connectivity networks into a highly distributed environment. Securing this ecosystem requires more than isolated security tools. Retail cybersecurity must operate as a coordinated architecture where each security layer validates identity, enforces policy, and maintains visibility across every connected device and location.
The S3M Security platform delivers an integrated security stack designed specifically for distributed operational environments like retail. Each product layer contributes to enforcing device trust, protecting payment systems, isolating customer connectivity, and maintaining centralized visibility across store networks.
Together, these layers create a unified architecture that protects retail infrastructure without disrupting operational agility.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
EndGuard evaluates device posture across traffic sensors, municipal workstations, and IoT endpoints embedded throughout city infrastructure. Trust is not static; it is continuously reassessed based on behavioral indicators and compliance posture.
In smart city environments where thousands of connected devices operate simultaneously, compromised endpoints can quickly become lateral access vectors. Posture-aware enforcement limits exposure while maintaining operational continuity.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
By combining identity-based access control, endpoint compliance enforcement, secure guest connectivity, and encrypted network infrastructure, retailers gain a resilient security architecture capable of protecting distributed store environments, payment systems, and customer connectivity at scale.
Security Outcomes That Enable Resilient Retail Operations
Retail organizations operate across distributed environments that include physical stores, warehouse facilities, corporate offices, and digital commerce platforms. Each of these environments introduces new security challenges involving customer connectivity, payment systems, employee mobility, and third-party vendor access.
Rather than relying on isolated security tools, modern retail infrastructure requires a coordinated security architecture designed to deliver measurable outcomes. Identity-driven network access control, real-time visibility, centralized policy enforcement, and controlled partner access work together to protect operations without disrupting business agility.
The S3M Security platform enables retailers to implement a comprehensive Zero Trust security strategy that strengthens protection across every store location, connected device, and user interaction.
Unified Security Control Plane
Secure Vendor and Partner Access
Regulatory Compliance Enablement
Scalable Security Governance
Continuous Infrastructure Visibility
Secure Public Connectivity
Zero Trust Enforcement
By aligning security architecture with operational outcomes such as Zero Trust enforcement, centralized governance, vendor access control, and regulatory compliance, retailers can confidently scale their digital infrastructure while maintaining secure and uninterrupted retail operations.
Retail Security FAQ
Retail environments combine high customer traffic, distributed store networks, payment infrastructure, and a constantly changing mix of connected devices. From POS terminals and inventory scanners to employee mobile devices and customer Wi-Fi, every connection introduces potential security risks if not properly controlled.
Retail security teams must maintain visibility, enforce access policies, and protect sensitive payment and operational systems without disrupting customer experience or store operations. This requires a security architecture capable of verifying device identity, controlling network access, and isolating guest connectivity across every retail location.
The following frequently asked questions address common concerns about retail cybersecurity, network access control, and Zero Trust security strategies used to protect modern retail infrastructure.
Why is network segmentation important in retail cybersecurity?
How can retailers safely offer guest Wi-Fi in stores?
How does Zero Trust improve security in retail environments?
How can retailers detect unauthorized devices on store networks?
How can retail chains manage security across hundreds of branches?
What role does endpoint security play in retail networks?
How can retailers protect payment card data from cyber threats?
Why is device visibility important in modern retail environments?
What are the benefits of unified network security in retail operations?
How can retailers secure large numbers of POS devices across stores?
Understanding how identity-driven security, device visibility, and controlled network access work together helps retail organizations build a resilient security architecture capable of protecting stores, customers, employees, and critical business systems.
Protect Retail Networks, Devices, and Customer Connectivity with Identity-Driven Security
Retail businesses operate in environments where connectivity is constant and security risks evolve quickly. Store networks support point-of-sale systems, inventory management platforms, digital signage, employee devices, and customer Wi-Fi services, all operating simultaneously within the same infrastructure.
Without strong network access control and visibility, unauthorized devices, compromised endpoints, or unsecured guest connections can introduce risks that impact payment systems, customer data, and operational continuity. Retail organizations require security solutions capable of protecting every store location while maintaining seamless customer and employee experiences.
S3M Security provides an identity-driven security architecture designed to protect distributed retail environments. By combining Zero Trust access control, real-time device visibility, and centralized policy enforcement, retailers gain the ability to secure their networks without disrupting day-to-day operations.
Discover how S3M Security helps retailers protect store infrastructure, secure customer connectivity, and maintain operational resilience across every retail location.
