BUILT FOR HYBRID ENTERPRISE INFRASTRUCTURE
Hybrid Enterprise Network Security Platform
Secure Every Connection. Orchestrate Every Access Layer.
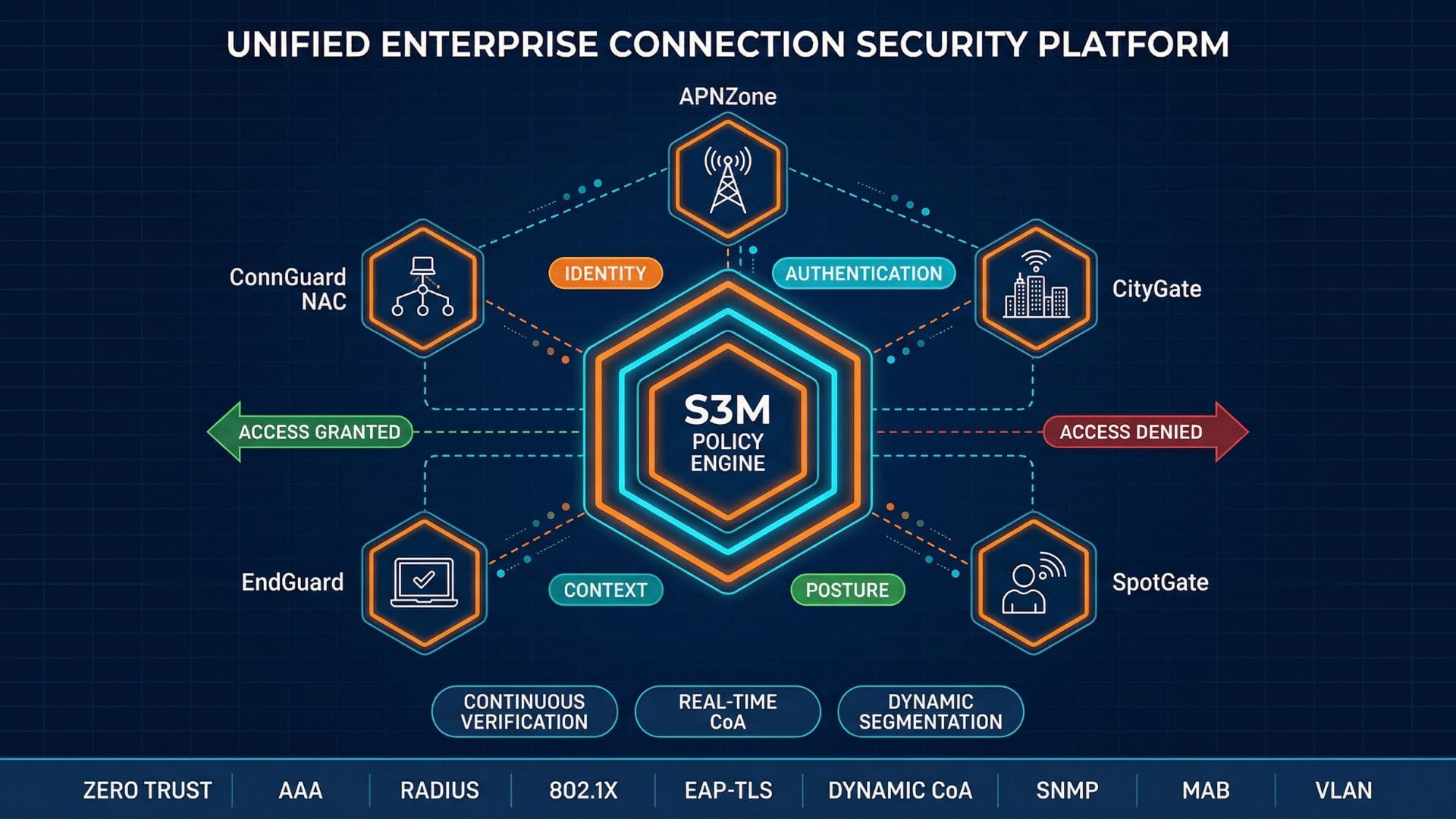
The S3M Hybrid Enterprise Network Security Platform redefines how modern organizations secure hybrid access environments.
By unifying Network Access Control, identity-based policy enforcement, endpoint posture validation and mobile APN security within a Zero Trust Network Architecture, enterprises eliminate fragmented controls and gain centralized orchestration across every connection domain.
Fragmented Security Models Undermine Zero Trust
Traditional access control architectures were designed for static networks.
Hybrid enterprise environments require unified enforcement across every connection layer.
Without centralized orchestration, Zero Trust becomes a policy statement—not an operational reality.
Identity Fragmentation
802.1X authentication may validate device access, but identity correlation across firewall, endpoint and mobile APN layers remains inconsistent.
Policy Inconsistency
Dynamic VLAN, RADIUS policies and Change of Authorization (CoA) events operate in isolation when systems are not unified.
Limited Hybrid Visibility
Cloud workloads, branch offices and unmanaged devices expand the attack surface beyond traditional NAC boundaries.
Evolving NAC into Enterprise Security Orchestration
Traditional Network Access Control solutions were originally designed to authenticate devices at the network edge. However, a Hybrid Enterprise Network Security Platform must go beyond basic authentication and instead enforce identity-driven policies across every connection domain.
While NAC remains foundational, modern enterprise security also requires advanced orchestration. Therefore, organizations must extend their security approach beyond simple access control and adopt a more unified, policy-driven framework.
From Port-Level Control to Identity-Based Enforcement
Early NAC implementations focused on 802.1X authentication and RADIUS-based access decisions at the switch port level.
While this model is effective for basic access validation, it primarily assumes static environments and isolated enforcement. However, modern enterprise infrastructures are highly dynamic; therefore, this limitation can lead to significant security gaps.
In hybrid infrastructures, identity must persist beyond the edge.
Access decisions must follow the user and device across wired, wireless and remote connections.
A modern Hybrid Enterprise Network Security Platform transforms NAC from a gatekeeper into a continuous identity enforcement layer.
Centralized Policy Engine as the Control Core
At the center of the architecture lies a unified policy engine that evaluates identity, posture, role and contextual signals in real time.
Instead of relying solely on static VLAN mapping, the platform applies:
Dynamic VLAN and ACL assignment
Real-time Change of Authorization (CoA)
Continuous device posture validation
Context-aware segmentation policies
This centralized enforcement model ensures consistency across LAN, Wi-Fi, firewall and mobile APN domains—strengthening Zero Trust Network Architecture implementation.
Unified Policy Engine for
Identity-Driven Enforcement
At the core of the Hybrid Enterprise Network Security Platform lies a centralized policy engine designed to enforce identity-driven access decisions in real time.
Rather than relying on static rule sets, the engine continuously evaluates authentication, authorization and contextual telemetry across hybrid infrastructure domains.
AAA-Based Decision Framework
The engine operates on a structured Authentication, Authorization and Accounting (AAA) framework.
It integrates with:
802.1X authentication services
RADIUS infrastructure
Active Directory or LDAP identity sources
Certificate-based EAP-TLS validation
Access decisions are not binary.
They are contextual, dynamic and continuously verified.
Context-Aware Policy Evaluation
The policy engine correlates multiple attributes before enforcing access:
User role and group membership
Device posture status
Network entry point (LAN, Wi-Fi, VPN, APN)
Behavioral risk indicators
Session-based telemetry
When posture degrades or risk signals change, the system triggers real-time Change of Authorization (CoA), dynamically updating VLAN or ACL assignments without disconnecting users.
This dynamic enforcement model strengthens Zero Trust Network Architecture implementation across distributed enterprise networks.
Hybrid Enforcement Model Built for Real-World Enterprise Networks
A Hybrid Enterprise Network Security Platform must secure both managed and unmanaged devices without compromising policy consistency.
Modern enterprise networks are heterogeneous by design. Enforcement must adapt accordingly.
Agent-Based Enforcement Layer
Designed for corporate endpoints, the agent-based layer enables:
Continuous posture validation
Certificate-based EAP-TLS enforcement
Operating system telemetry collection
Real-time risk signaling
This layer ensures granular, identity-driven enforcement at the device level.
Agentless Network Control
For IoT, printers and unmanaged systems, enforcement relies on:
MAC-based authentication (MAB)
Device fingerprinting
Switch-level SNMP visibility
Dynamic RADIUS segmentation
This ensures policy coverage without operational friction.
Identity Persistence
Dynamic VLAN Enforcement
Real-Time CoA Updates
Cross-Domain Segmentation
Adaptive Enforcement Across Hybrid Enterprise Networks
A Hybrid Enterprise Network Security Platform must respond to posture degradation and behavioral anomalies in real time. Therefore, it can continuously adapt security controls based on evolving risk signals and contextual insights.
However, static access models are insufficient in dynamic enterprise environments; instead, organizations must adopt continuous validation and adaptive enforcement mechanisms. As a result, security becomes more resilient, responsive, and aligned with modern threat landscapes.
Real-Time Change of Authorization (CoA)
When device posture changes or risk signals increase, the platform triggers immediate Change of Authorization events without forcing user disconnection.
Dynamic Segmentation Enforcement
VLAN and ACL policies update dynamically based on identity and context, reducing lateral movement risk across hybrid infrastructure.
Integrated Security Ecosystem
The policy engine synchronizes with firewall, SIEM and endpoint platforms, enabling cross-domain enforcement decisions.
Operational Risk Containment
Compromised or non-compliant endpoints can be quarantined automatically while maintaining business continuity for compliant systems.
Enterprise-Grade Deployment Flexibility
A Hybrid Enterprise Network Security Platform must integrate seamlessly into existing infrastructure while also remaining scalable across distributed environments. Therefore, organizations can extend their security capabilities without introducing unnecessary complexity.
Moreover, security modernization should not require a complete architectural replacement; instead, it should enhance and evolve the current infrastructure. As a result, enterprises can achieve stronger security outcomes while maintaining operational continuity.
On-Prem & Hybrid Deployment
The platform supports virtual appliances, clustered architectures and distributed enforcement nodes across branch and core environments.
Multi-Tenant Architecture
Segregated policy domains enable service providers and large enterprises to manage multiple business units under a unified policy framework.
Vendor-Agnostic Integration
Compatibility with heterogeneous network infrastructure ensures organizations retain existing investments while modernizing access control.
A scalable architecture ensures consistent enforcement across enterprise, branch, and mobile infrastructure; therefore, organizations can maintain unified security policies without fragmentation.
Moreover, this approach reduces operational complexity while enabling seamless expansion across distributed environments.
Reimagining Enterprise Access Security for the Hybrid Era
The Hybrid Enterprise Network Security Platform by S3M transforms traditional Network Access Control into a unified, identity-driven orchestration layer. As a result, organizations can move beyond fragmented security models and adopt a more cohesive approach.
Moreover, by consolidating authentication, posture validation, and dynamic enforcement within a Zero Trust Network Architecture, enterprises gain enhanced visibility, improved consistency, and adaptive protection across every connection domain. Consequently, security operations become more proactive and resilient.
Therefore, security is no longer just about controlling ports; instead, it is about orchestrating trust across the entire infrastructure.
Frequently Asked Questions
What makes a Hybrid Enterprise Network Security Platform different from traditional NAC?
Answer:
A traditional Network Access Control system focuses primarily on authentication at the network edge. A Hybrid Enterprise Network Security Platform extends enforcement beyond port-level validation by integrating identity correlation, posture assessment and dynamic segmentation within a Zero Trust Network Architecture.
How does hybrid enforcement improve Zero Trust implementation?
Answer:
Hybrid enforcement combines agent-based posture validation for managed endpoints with agentless visibility for unmanaged devices. This ensures consistent identity-driven access control across wired, wireless and mobile infrastructure.
Does the platform support 802.1X and RADIUS integration?
Answer:
Yes. The policy engine integrates with 802.1X authentication services, RADIUS infrastructure and directory-based identity sources, enabling dynamic VLAN assignment and real-time Change of Authorization (CoA).
Can the platform operate in multi-tenant environments?
Answer:
The architecture supports segregated policy domains, allowing enterprises and service providers to manage multiple business units or customers under a unified security framework.
Explore Related Architecture Layers
Hybrid NAC Architecture
Deep dive into hybrid enforcement models combining agent-based and agentless policy control.
Vendor-Agnostic NAC Integration
Learn how unified policy engines operate across heterogeneous network infrastructure.
Zero Trust Network Access Control
Understand how identity-driven enforcement strengthens Zero Trust Network Architecture.