Healthcare Network Security Architecture
Identity-Driven Zero Trust Security for Hospitals,
Medical Devices and Clinical Infrastructure
Healthcare infrastructure has evolved into a highly connected digital ecosystem.
Hospitals now rely on electronic health record systems, connected medical devices, diagnostic platforms, telemedicine services and remote clinical networks.
However, traditional perimeter-based security models cannot protect healthcare environments where clinicians, devices, vendors and patients constantly interact across distributed infrastructure.
S3M Security enables identity-driven Zero Trust architecture designed to secure hospital networks, protect patient data and enforce policy across connected medical systems
The Structural Security Risks in
Modern Healthcare Infrastructure
Healthcare organizations operate one of the most complex digital infrastructures of any industry. Hospitals run thousands of connected systems including medical imaging platforms, clinical workstations, patient monitoring devices and laboratory systems.
Despite this complexity, many healthcare networks still rely on security models originally designed for traditional enterprise environments. As hospitals continue to digitize operations, this mismatch between infrastructure complexity and security architecture introduces significant risk.
Without identity-driven visibility and access control, medical devices, users and external partners can create uncontrolled access paths across clinical networks.
Unmanaged Medical Devices
Thousands of connected medical devices operate across hospital networks without centralized identity validation or security monitoring.
Clinical Network Visibility Gaps
Healthcare IT teams often lack full visibility into connected clinical systems, imaging devices and laboratory infrastructure.
Lateral Movement Risks
Once inside a hospital network, attackers can move laterally between clinical systems, administrative networks and sensitive patient databases.
Third-Party Vendor Access
External vendors frequently require remote access to hospital systems for maintenance, updates and diagnostics.
Patient Data Compliance Pressure
Healthcare organizations must protect sensitive patient information while complying with strict regulatory frameworks.
Protecting modern healthcare infrastructure requires more than isolated security tools.
It requires a unified architecture capable of continuously validating identities, controlling access across clinical systems, and securing the complex digital environments hospitals depend on every day.
Security Challenges
Why Traditional Security Models Fail in Healthcare Networks
Healthcare environments have evolved into highly connected digital ecosystems where clinicians, medical devices, clinical applications and external vendors continuously interact.
However, many hospital networks still rely on security models originally designed for static enterprise environments. These legacy approaches struggle to protect modern healthcare infrastructure where identities, devices and access points constantly change.
Without identity-driven enforcement, traditional security models cannot provide the visibility and control required to secure clinical systems and patient data.
Perimeter-Based Security
Traditional hospital security models focus on protecting network perimeters. However healthcare infrastructure extends far beyond a single network boundary.
Static Network Segmentation
VLAN-based segmentation does not prevent lateral movement when device identity and access context are not continuously verified.
Medical Device Blind Spots
Many healthcare networks lack visibility into connected medical devices, leaving large portions of clinical infrastructure unmanaged.
Uncontrolled Vendor Access
External vendors often require access to hospital systems, creating additional attack surfaces when identity validation is not enforced.
Regulatory Environment
Healthcare Cybersecurity is Driven
by Regulatory Accountability
Healthcare organizations operate under some of the most demanding regulatory frameworks of any industry.
Hospitals and medical institutions must ensure strict protection of patient data, maintain traceable access to clinical systems and continuously monitor network activity across complex digital infrastructure.
Regulatory frameworks such as HIPAA, GDPR and ISO 27001 require healthcare providers to implement strong access controls, device visibility and detailed audit trails across healthcare networks.
These requirements place significant pressure on healthcare IT teams to maintain security visibility across thousands of medical devices, clinical workstations and third-party vendor systems.
HIPAA Compliance
The Health Insurance Portability and Accountability Act requires strict safeguards to protect patient health information across healthcare systems.
GDPR
Healthcare providers operating internationally must comply with strict data protection and patient privacy regulations.
ISO 27001
Healthcare organizations adopt ISO 27001 frameworks to establish structured information security management processes.
NIS2 Directive
The NIS2 directive strengthens cybersecurity requirements for critical healthcare infrastructure across Europe.
Security Architecture
Identity-Driven Security Architecture for
Healthcare Networks
Healthcare infrastructure requires a security architecture capable of protecting clinical systems, connected medical devices and sensitive patient data across highly distributed environments.
S3M Security implements a Zero Trust architecture that continuously verifies identities, segments network access and maintains full visibility across hospital infrastructure.
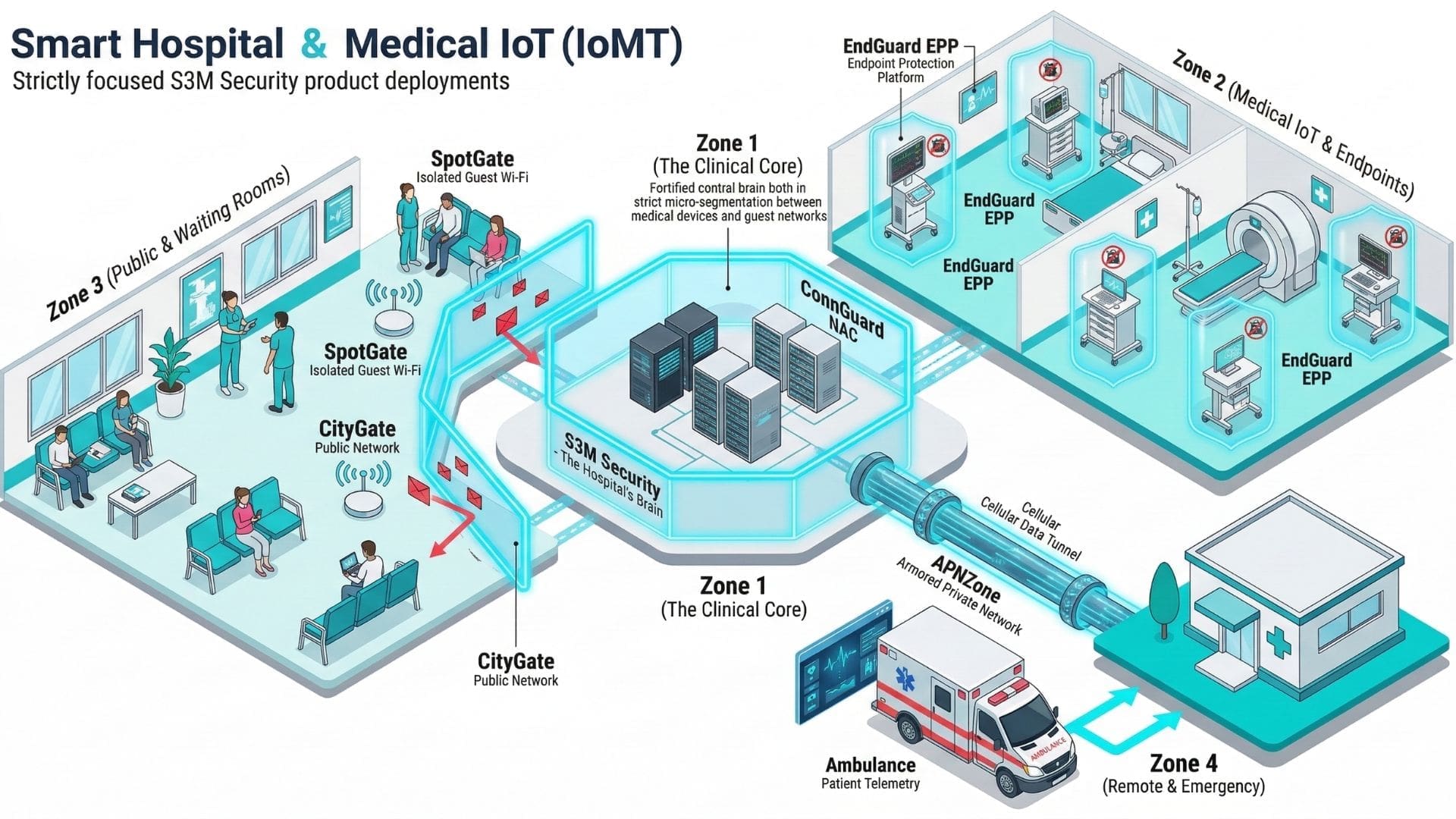
Identity Verification
Every clinician, device and system connecting to the network is continuously authenticated and validated before gaining access.
Network Access Control
Devices and users are dynamically segmented across healthcare networks to prevent unauthorized lateral movement.
Medical Device Protection
Every clinician, device and system connecting to the network is continuously authenticated and validated before gaining access.
Continuous Visibility
Healthcare security teams maintain real-time visibility across clinicians, systems and infrastructure activity.
Architecture in Action: Healthcare Security Scenarios
A security architecture only proves its value when it protects real clinical environments. The following scenarios demonstrate how identity-driven network enforcement secures hospital infrastructure, connected medical devices and sensitive patient data.
Protecting Sensitive Patient Data Across Systems
Scenario
Threat
Architectural Response
Operational Impact
Hospital Staff Mobility Across Facilities
Scenario
Threat
Architectural Response
Operational Impact
Telemedicine and Remote Clinical Access
Scenario
Threat
Architectural Response
Operational Impact
Third-Party Vendor Maintenance Access
Scenario
Threat
Architectural Response
Operational Impact
Electronic Health Record System Access
Scenario
Threat
Architectural Response
Operational Impact
Connected Medical Devices Across Clinical Networks
Scenario
Threat
Architectural Response
Operational Impact
Identity-driven security enables healthcare organizations to protect clinical infrastructure while maintaining uninterrupted patient care.
Operational Security Use Cases
The following operational capabilities demonstrate how identity-driven access control and network segmentation secure modern healthcare environments. Each use case illustrates how S3M Security architecture protects hospital networks, connected medical devices and sensitive patient data across clinical infrastructure.
Guest Network Isolation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Remote Workforce
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Critical Infrastructure Segmentation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Vendor Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Supply Chain Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Network Visibility
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure BYOD
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Unmanaged Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IDENTITY-DRIVEN NETWORK CONTROL ENABLES SECURE AND RESILIENT HEALTHCARE DIGITAL INFRASTRUCTURE.
Architecture Components
Supporting Healthcare Security
Each architecture component contributes to enforcing identity-driven security across hospital networks, connected medical devices and distributed healthcare infrastructure.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
A layered security architecture proves its value when protecting real clinical environments. The following components demonstrate how identity-driven enforcement secures healthcare systems, medical devices and sensitive patient data across modern hospital infrastructure.
Strategic Security Outcomes for
Healthcare Organizations
Modern healthcare cybersecurity must deliver more than isolated security controls. Hospitals require a unified architecture capable of protecting patient data, securing connected medical devices and maintaining visibility across complex clinical infrastructure.
Identity-driven network security enables healthcare organizations to enforce consistent access control, strengthen compliance and reduce operational risk across hospital environments.
Secure Workforce Mobility
Operational Continuity
Regulatory Compliance Enablement
Unified Security Control Plane
Zero Trust Enforcement
Secure Public Connectivity
When security architecture aligns with clinical operations, healthcare organizations gain both resilience and operational confidence.
