Identity-Driven Security for Logistics & Supply Chain
Logistics Cybersecurity Architecture for Distributed Supply Chains
Modern logistics infrastructure is no longer confined to warehouses or fixed networks.
Fleet operations, IoT-enabled facilities, third-party integrations, and cross-border data flows create a highly distributed and continuously moving attack surface.
Traditional perimeter-based security models cannot control or secure this environment.
S3M delivers an identity-driven Zero Trust architecture designed to secure logistics ecosystems across fleets, warehouses, and global supply chain networks — where identity, not location, defines access.
RISK LANDSCAPE
The Structural Risk Behind Logistics Network Expansion
Modern logistics ecosystems are no longer confined to warehouses and distribution centers. They operate across fleets, mobile assets, IoT-enabled tracking systems, partner networks, and real-time data platforms.
However, security architectures have not evolved at the same speed. Many logistics organizations still rely on perimeter-based models that fail to address distributed infrastructure, mobile endpoints, and identity-less network access.
As logistics operations become more connected and time-sensitive, visibility gaps increase. Security teams struggle to maintain real-time control over who and what is accessing critical systems across regions, fleets, and third-party integrations.
- Unsecured fleet connectivity across regions
- Unmanaged IoT tracking and telematics devices
- Third-party logistics partner access risks
- Lack of real-time identity visibility across networks
- Increasing compliance pressure (GDPR, ISO 27001, transport regulations)
Logistics infrastructure now requires identity-driven network security architecture — not perimeter-based assumptions.
LIMITATIONS OF TRADITIONAL SECURITY
Perimeter-Based Security Cannot Protect Distributed Logistics Networks
Traditional network security models were designed for static environments — centralized data centers, fixed users, and clearly defined network boundaries. Logistics operations today operate in a completely different reality.
No Defined Network Perimeter
Logistics environments extend beyond physical locations into fleets, partner systems, and cloud services. The concept of a fixed network boundary no longer exists.
Unmanaged Device Diversity
From telematics units and handheld scanners to personal mobile devices, logistics networks include thousands of unmanaged and unverified endpoints.
Lack of Identity-Based Access Control
Traditional systems focus on network location rather than identity. This makes it impossible to verify who or what is accessing critical logistics systems in real time.
Inability to Scale Across Regions
Global logistics operations require consistent security policies across warehouses, distribution hubs, and transport networks — something legacy systems cannot deliver.
No Real-Time Visibility
Security teams lack continuous visibility into device behavior, access patterns, and network interactions, creating blind spots across operations.
Compliance Gaps in Dynamic Environments
Static security models cannot meet evolving regulatory requirements such as GDPR, transport regulations, and lawful logging obligations in distributed infrastructures.
Without an identity-driven architecture, logistics organizations cannot control access, enforce policy, or maintain compliance across modern distributed operations.
SECURITY ARCHITECTURE
Identity-Driven Network Security for Distributed Logistics Infrastructure
Modern logistics environments require a shift from location-based trust to identity-based control. Every connection — whether from a warehouse system, fleet device, partner network, or mobile user — must be verified, validated, and continuously monitored.
An effective logistics security architecture must operate across distributed environments without relying on fixed boundaries. It should enforce identity-based access, dynamically segment network traffic, and ensure that every device and user is continuously evaluated based on behavior and context.
This approach enables organizations to secure fleet connectivity, warehouse operations, IoT tracking systems, and third-party integrations within a unified policy framework — without introducing operational friction.
Security becomes an embedded operational layer — not a bottleneck.
Identity-Based Access Control
Every user, device, and system is authenticated and authorized based on identity, not network location.
Dynamic Micro-Segmentation
Network access is segmented in real time, isolating critical logistics systems from unauthorized or risky entities.
Continuous Visibility & Monitoring
All connections, behaviors, and access patterns are tracked continuously across distributed infrastructure.
Secure Remote & Fleet Access
Fleet systems, mobile users, and remote operations connect through encrypted and policy-controlled channels.
This architecture enables logistics organizations to scale securely, maintain compliance, and operate with full control over distributed network environments.
ARCHITECTURE DIAGRAM
Zero Trust Architecture for Logistics Network Environments
A modern logistics security architecture must operate across distributed environments — from warehouses and fleet systems to cloud platforms and partner integrations — without relying on traditional network boundaries.
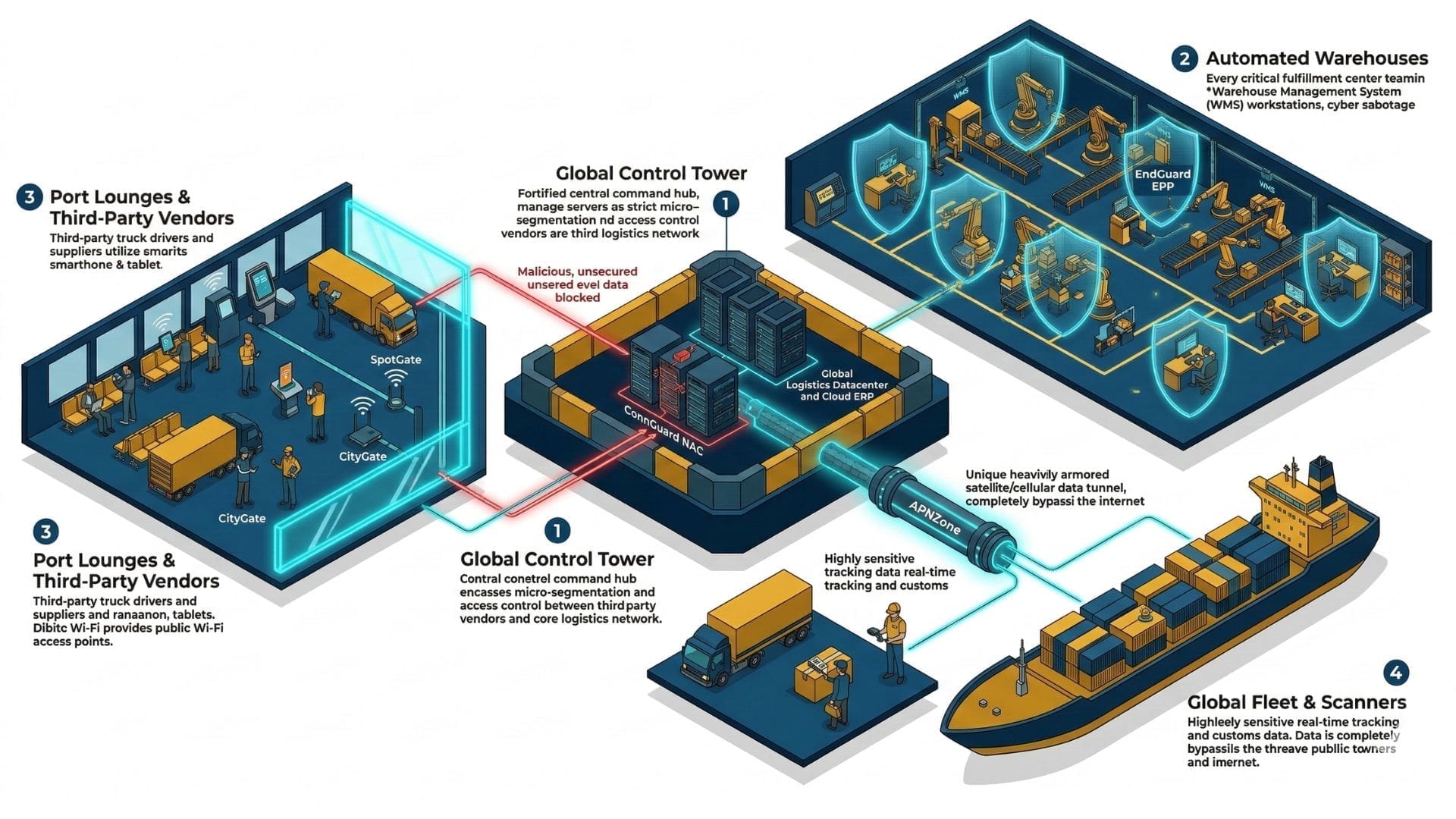
Identity Control Layer
All users, devices, and systems are authenticated before accessing any logistics resource.
Device Intelligence Layer
IoT devices, fleet systems, and endpoints are continuously profiled and evaluated.
Network Segmentation Layer
Dynamic segmentation isolates critical systems such as warehouse operations and transport networks.
Secure Access Layer
Encrypted and policy-driven access ensures secure connectivity across regions and remote environments.
Visibility & Monitoring Layer
All network activity is monitored in real time to detect anomalies and enforce compliance.
Partner Access Control
Third-party logistics providers are granted controlled and isolated access based on policy.
Fleet Connectivity Security
Vehicles and mobile systems connect securely through controlled and encrypted channels.
Compliance & Logging Layer
All access and activity logs are recorded to meet GDPR and regulatory requirements.
This layered architecture ensures that logistics operations remain secure, scalable, and compliant across complex and distributed infrastructures.
INDUSTRY SCENARIOS
Real-World Logistics Security Scenarios
Logistics operations face security challenges that evolve across fleets, warehouses, partner networks, and global supply chains. These scenarios illustrate how identity-driven architecture responds to real operational risks.
Remote Access Vulnerability
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
IoT Tracking Manipulation
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Third-Party Logistics Access Risk
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Warehouse Device Compromise
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
Fleet Connectivity Breach
SCENARIO
THREAT
ARCHITECTURAL RESPONSE
OPERATIONAL IMPACT
OPERATIONAL USE CASES
How Security Architecture Operates Across Logistics Environments
Beyond high-level architecture, logistics organizations require security systems that operate seamlessly across real environments — fleets, warehouses, IoT ecosystems, and partner integrations.
Fleet Device Authentication
All fleet-connected devices are authenticated before accessing central logistics systems, ensuring that only trusted endpoints participate in operations.
Warehouse Network Segmentation
Warehouse systems are dynamically segmented, isolating operational technologies from administrative and external access.
Secure Partner System Integration
Third-party logistics providers are granted controlled, policy-based access to specific systems without exposing core infrastructure.
IoT Device Validation
Tracking and telematics devices are continuously monitored and validated to detect anomalies and prevent data manipulation.
Remote Workforce Access Control
Remote operators connect through secure, encrypted channels with identity verification and device posture checks.
Real-Time Network Visibility
Security teams maintain continuous visibility into all network activity, enabling rapid detection and response.
A Layered Security Architecture for Logistics Operations
Modern logistics environments require multiple security layers working together — from identity control and endpoint validation to secure connectivity and lawful access management. Each layer addresses a specific operational risk while contributing to a unified architecture.
Secure Connectivity Layer
Fleet systems, telematics devices, and remote logistics operations require secure and uninterrupted connectivity across distributed environments.
SIM-based devices connect through encrypted and private tunnels, completely isolated from the public internet. This ensures that data flows securely between field operations and central systems without exposure to external threats.
ENABLING TECHNOLOGIES
Endpoint Compliance Layer
Every device attempting to connect to the network is evaluated against security policies before access is granted. This includes validation of antivirus status, operating system updates, and overall device posture.
Devices that do not meet compliance requirements or show signs of compromise are automatically denied access, preventing endpoint-based threats from spreading across logistics operations.
ENABLING TECHNOLOGIES
Guest & External Access Layer
Logistics environments involve constant movement of external users such as drivers, temporary staff, auditors, and partners. These access points must be controlled without exposing internal systems.
Guest access is fully isolated from the corporate network. Authentication mechanisms such as SMS or email verification ensure controlled connectivity, while all sessions are logged in compliance with regulatory requirements.
ENABLING TECHNOLOGIES
Identity & Access Control Layer
Manage hundreds of distributed warehouse devices, barcode scanners, and handheld terminals from a centralized control point. Gain real-time visibility into what is connected to your network, where it is located, and who is using it.
Every device is continuously authenticated and evaluated based on identity. Unauthorized, unverified, or risky devices — including threats such as MAC spoofing — are automatically blocked or isolated before they can impact operations.
ENABLING TECHNOLOGIES
Together, these layers form a unified, identity-driven security architecture that protects logistics operations at scale — without introducing friction or slowing down critical processes.
Business Outcomes of an Identity-Driven Logistics Security Architecture
Adopting an identity-driven security architecture enables logistics organizations to move beyond reactive protection and establish full operational control across distributed environments. Security becomes a business enabler — not a limitation.
Unified Security Control Plane
Secure Vendor and Partner Access
Secure Workforce Mobility
Scalable Security Governance
This architecture transforms security into a strategic capability — enabling logistics organizations to scale, operate, and innovate with confidence.
