Smart City Network Security Architecture
Identity-Driven Zero Trust for
Municipal Infrastructure and Public Connectivity
Modern cities rely on public WiFi, IoT sensors, transportation systems, and distributed digital services.
However, perimeter-based security models cannot protect city-scale infrastructure.
S3M delivers identity-enforced, Zero Trust architecture designed for municipal networks and smart city environments.
The Structural Risk Behind
Smart City Expansion
Smart city infrastructure is no longer experimental. It is operational, distributed, and deeply embedded into transportation systems, public WiFi networks, utilities, surveillance grids, and citizen-facing digital services.
However, security architecture has not evolved at the same pace. Many municipalities still rely on perimeter-based controls designed for centralized enterprise networks — not for distributed, identity-less, city-scale connectivity.
As public connectivity expands and IoT endpoints multiply across districts, visibility gaps widen. Municipal IT teams often lack real-time clarity on identity, device posture, and lateral access paths.
As public connectivity expands and IoT endpoints multiply across districts, visibility gaps widen. Municipal IT teams often lack real-time clarity on identity, device posture, and lateral access paths.

Smart city infrastructure now requires identity-enforced network architecture — not perimeter-based trust assumptions.
- Identity-less public WiFi sessions across districts
- Unmanaged IoT sensors embedded in traffic and utility grids
- Lateral exposure between municipal departments
- Increasing regulatory pressure (GDPR, 5651, ISO 27001)
- Limited real-time network visibility at city scale
Why Perimeter-Based Security No Longer Works
Traditional municipal security models were designed around static network boundaries. However, smart city ecosystems are fluid, distributed, and identity-driven. The mismatch creates structural exposure.
Firewall-Centric Thinking
Firewalls were designed to protect fixed perimeters. In a smart city, connectivity originates from distributed IoT endpoints, mobile users, and public access nodes beyond traditional boundaries.
Static VLAN Segmentation
Segmenting networks by department does not prevent lateral movement when identity is not continuously verified. VLAN-based trust models assume internal safety — a flawed assumption at city scale.
IP-Based Policy Models
IP addresses no longer represent identity. Devices change networks, mobile assets move across districts, and public WiFi sessions rotate dynamically. Policy must follow identity, not IP allocation.
Manual Onboarding Dependencies
Manual device onboarding and sponsor-based approvals introduce operational bottlenecks. City-scale infrastructure requires automated identity validation and dynamic policy orchestration.
Smart City Network Security Architecture
Traditional municipal security models were designed around static network boundaries. However, smart city ecosystems are fluid, distributed, and identity-driven. The mismatch creates structural exposure.
Compliance Exposure Points
Public WiFi log retention requirements
Citizen data protection mandates
IoT device auditability
Cross-department traffic accountability
Real-time access traceability
Regulatory Framework Examples
GDPR (EU Data Protection Regulation)
5651 (Turkey Internet Law & Logging Obligations)
ISO 27001 (Information Security Management)
NIS2 (Network & Information Security Directive)
National critical infrastructure protection standards
Municipal cybersecurity architecture must not only protect infrastructure — it must also demonstrate accountability under audit.
An Identity-Driven Security Architecture for Smart Cities
Smart city ecosystems require continuous identity validation across users, devices, applications, and infrastructure layers. Security must operate as an architectural control plane — not as an isolated product layer.
Identity Access Layer
Identity becomes the primary enforcement mechanism across smart city infrastructure. Every user, device, and service must be authenticated and continuously validated before access is granted.
Access decisions follow identity, not network location.
Endpoint & Device Posture Layer
Devices are evaluated based on compliance state, behavioral indicators, and operational context. Trust is dynamic, not permanent.
Device posture directly influences network segmentation and access privileges.
Public Connectivity Governance Layer
Public WiFi sessions are isolated, logged, and policy-controlled to prevent lateral exposure into municipal systems.
Guest access must remain auditable and structurally separated from operational infrastructure.
Mobile & Distributed Infrastructure Layer
Field assets, IoT sensors, and remote systems operate through encrypted and policy-enforced channels beyond physical network boundaries.
Security enforcement extends beyond physical perimeters into mobile and carrier environments.
Carrier-Grade Orchestration Layer
Policy decisions are synchronized across access points, districts, data centers, and cloud environments to ensure architectural consistency.
Centralized orchestration eliminates fragmented security controls across city infrastructure.
Smart city security must function as an integrated architectural model — not as fragmented point solutions layered onto legacy infrastructure.
Architecture in Action: Smart City Operational Scenarios
A layered architecture only proves its value when it operates under real-world pressure. The following scenarios illustrate how identity-driven enforcement reshapes municipal cybersecurity outcomes.
Mobile Municipal Workforce & Distributed Assets
Scenario
Threat
Architectural Response
Operational Impact
Connected Traffic & Utility Sensors
Scenario
Threat
Architectural Response
Operational Impact
Public WiFi Expansion Across Municipal Districts
Scenario
Threat
Architectural Response
Operational Impact
Smart city cybersecurity must function dynamically under operational pressure — not only under theoretical architectural design.
Security Outcomes for Defense & Military Infrastructure
Modern defense infrastructures require cybersecurity architectures that not only prevent attacks but also strengthen operational resilience. By implementing identity-driven access control, secure connectivity and infrastructure segmentation, defense organizations gain strategic advantages that directly impact mission readiness and operational security.
Guest Network Isolation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Critical Infrastructure Segmentation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Supply Chain Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure BYOD
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Public Connectivity Infrastructure
Scenario
Threat
Architectural Response
Operational Impact
Security Components
These strategic outcomes enable defense organizations to operate highly connected infrastructures while maintaining strict operational security and mission resilience.
Architecture Components
Supporting Smart City Security
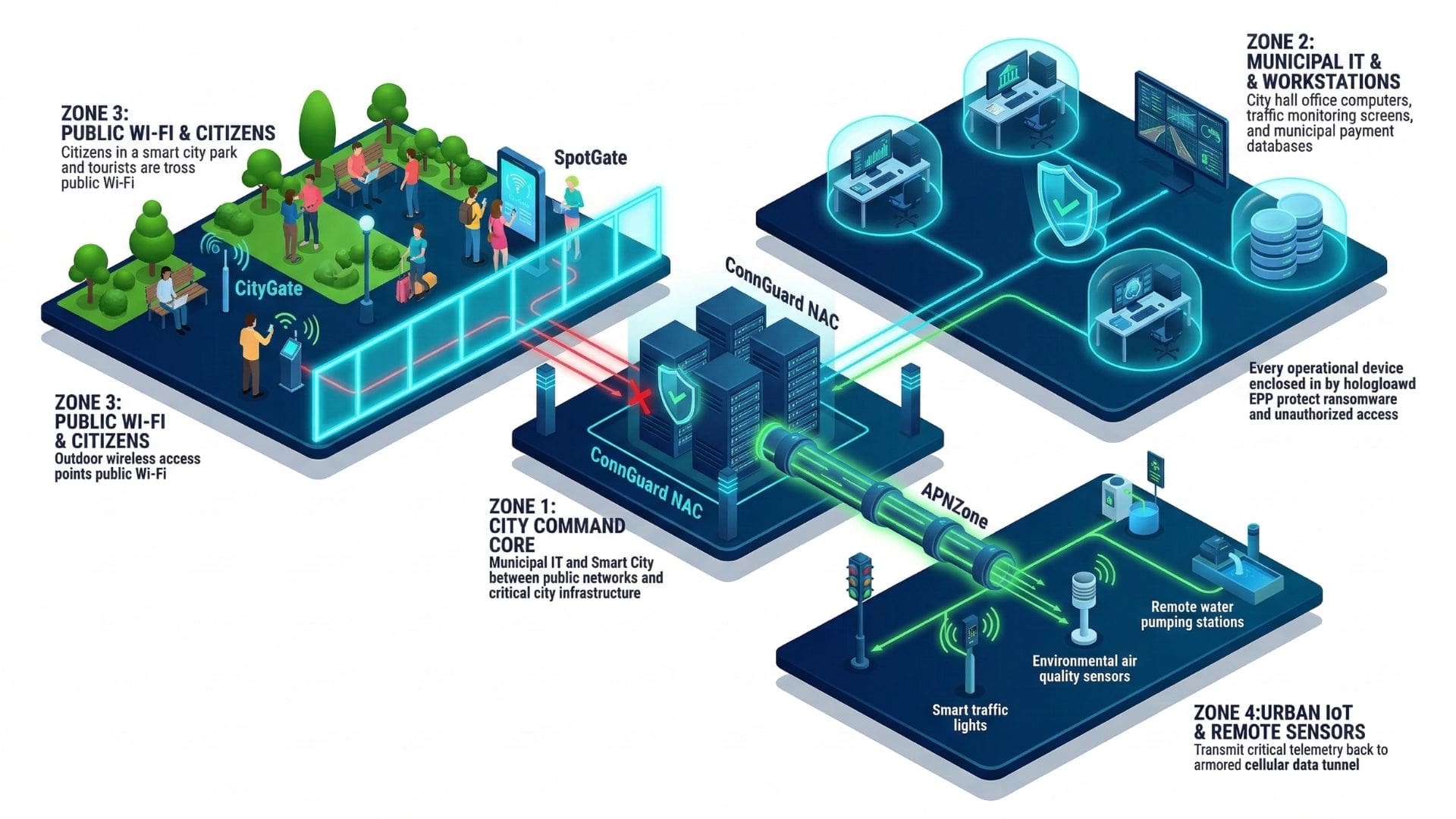
Each architecture component contributes to enforcing identity-driven security across distributed urban infrastructure.
Role Description
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
A layered architecture only proves its value when it operates under real-world pressure. The following scenarios illustrate how identity-driven enforcement reshapes municipal cybersecurity outcomes.
Strategic Security Outcomes
Identity-driven network control enables municipalities to operate complex digital infrastructure securely while maintaining operational agility and citizen accessibility.
