Hospitality Network Security Architecture
Hotels, resorts, stadiums, and entertainment venues operate some of the most complex connectivity environments in modern infrastructure. Thousands of guests, staff devices, IoT systems, and payment platforms connect simultaneously across distributed networks.
Traditional perimeter security models cannot protect hospitality environments where guest access, mobile devices, and temporary infrastructure constantly change.
S3M Security delivers identity-driven network security architecture designed for hospitality environments — enabling secure guest connectivity, protected operational networks, and continuous visibility across large venues.
The Structural Risk Behind Hospitality Connectivity
Modern hospitality environments operate as high-density digital ecosystems where thousands of devices connect across guest WiFi, smart rooms, building systems, conference infrastructure, and operational platforms.
Hotels, resorts, stadiums, and large venues must support continuous connectivity for guests, staff members, mobile operations, and automated infrastructure. As these networks expand, the traditional concept of a secure internal perimeter becomes increasingly difficult to maintain.
Unlike traditional enterprise environments, hospitality infrastructure must handle unpredictable device populations. Every day, thousands of new devices connect to guest networks without prior registration or device management.
This constant churn creates significant visibility gaps for IT teams attempting to identify users, validate devices, and enforce consistent access policies across distributed venues.
At the same time, hospitality environments rely on operational systems that must remain isolated from public connectivity, including payment platforms, building automation, security surveillance networks, and internal operational services.
Without identity-driven network controls, attackers can exploit guest connectivity environments as entry points into operational infrastructure.
- High-volume guest WiFi sessions across hotels, resorts, and event venues
- Unmanaged personal devices connecting to hospitality networks
- IoT infrastructure embedded in smart rooms and building automation systems
- Payment terminals and POS systems operating on shared network infrastructure
- Limited visibility into device identity and network behavior
- Growing regulatory pressure around guest data protection and network logging
Hospitality organizations require identity-driven network security architecture capable of managing thousands of transient devices while protecting operational infrastructure from lateral exposure.
Why Traditional Hospitality Security Models Break at Scale
Hospitality infrastructure operates under conditions fundamentally different from corporate enterprise networks. Hotels, resorts, stadiums, and entertainment venues must support thousands of transient devices, guest connections, and distributed operational systems.
Legacy network security models were designed around fixed users, managed devices, and predictable network boundaries. Hospitality environments operate without these assumptions.
As a result, traditional perimeter security approaches introduce operational blind spots that increase exposure across guest networks, IoT infrastructure, and venue operations.
Legacy Network Security Model
- Firewall-Centric Protection
Traditional security architectures rely on perimeter firewalls to protect internal infrastructure. Hospitality networks extend beyond a single boundary as guest devices and event systems continuously join the network.
- Static VLAN Segmentation
Many hospitality environments separate guest and operational networks using static segmentation. Without identity verification, segmentation alone cannot prevent lateral movement.
- IP-Based Access Policies
IP addresses do not represent identity in hospitality environments. Devices constantly move between access points, networks, and venues.
- Manual Device Management
Hospitality IT teams cannot manually onboard thousands of guest devices, conference systems, and temporary infrastructure components every day.
Identity-Driven Security Architecture
- Identity-Based Access Enforcement
Every device and user connecting to hospitality infrastructure must be authenticated and validated before network access is granted.
Access policies follow identity and device posture rather than network location.
- Dynamic Network Segmentation
Network segmentation becomes dynamic and policy-driven, automatically isolating guest devices, IoT infrastructure, and operational systems.
- Continuous Device Trust Evaluation
Devices are evaluated based on posture, behavioral signals, and operational context before receiving network privileges.
- Automated Infrastructure Onboarding
Security architecture must support automated onboarding for guest devices, IoT systems, and event infrastructure.
Hospitality environments require identity-driven network security architecture capable of protecting guest connectivity without exposing operational infrastructure.
Hospitality Network Security Architecture
Hospitality environments require a security architecture capable of protecting both public connectivity environments and critical operational systems. Hotels, resorts, stadiums, and large venues must simultaneously support thousands of guest devices while ensuring that payment systems, operational infrastructure, and internal services remain isolated and protected.
S3M Security delivers an identity-driven Zero Trust architecture designed to enforce security policies across hospitality infrastructure without disrupting guest connectivity or operational services.
Operational Exposure Points
- High-density guest WiFi networks across hotels and venues
- Unmanaged personal devices connecting to hospitality infrastructure
- Smart room IoT devices integrated into building systems
- Payment infrastructure and POS networks operating across venues
- Limited visibility into device identity and network access behavior
Compliance & Regulatory Framework
- PCI DSS — payment infrastructure protection
- GDPR — guest data privacy compliance
- ISO 27001 — information security governance
- Regional internet logging regulations
- Hospitality infrastructure security policies
Hospitality cybersecurity architecture must protect guest connectivity without exposing operational infrastructure. Identity-driven security enforcement enables hotels and large venues to maintain open digital environments while maintaining strict control over network access and infrastructure visibility.
Identity-Driven Security Architecture
for
Hospitality Infrastructure
Hospitality infrastructure requires continuous identity validation across users, devices, applications, and operational systems. Security must function as an architectural control layer rather than a single perimeter defense mechanism.
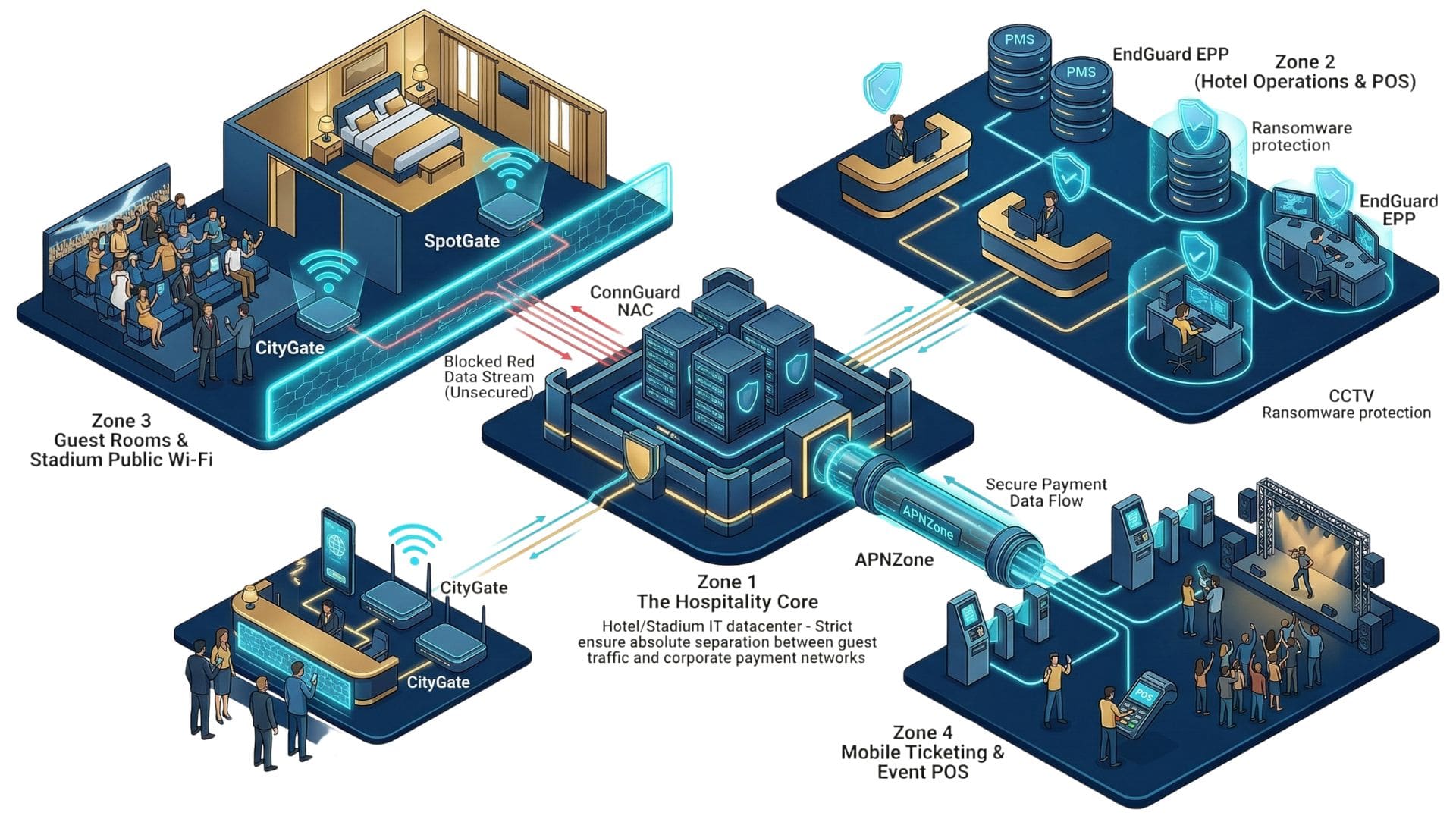
S3M Security delivers a layered architecture designed to secure hospitality environments including guest WiFi networks, smart room IoT devices, payment infrastructure, and distributed venue connectivity.
Identity Access Layer
Identity becomes the primary enforcement mechanism across hospitality infrastructure. Every user, device, and operational service must be authenticated and continuously validated before receiving network access.
Access decisions follow identity rather than network location.
Powered by ConnGuard NAC
Endpoint & Device Posture Layer
Devices connecting to hospitality infrastructure are evaluated based on security posture, behavior signals, and operational context.
Compromised or non-compliant devices can be isolated automatically before reaching operational systems.
Implemented with EndGuard EPP
Guest Connectivity Governance Layer
Guest WiFi access is isolated, authenticated, and policy-controlled to prevent exposure to internal hospitality infrastructure.
Captive portals, identity validation, and session monitoring enable secure guest connectivity at scale.
Implemented with SpotGate
Distributed Infrastructure Security Layer
Hospitality infrastructure often extends across multiple buildings, venues, and event environments. Remote systems, mobile infrastructure, and IoT devices must connect through encrypted and policy-controlled communication channels.
Implemented with APNZone
Centralized Security Orchestration Layer
Security policies must operate consistently across hotels, resorts, and large venues. Centralized orchestration ensures visibility, policy enforcement, and compliance monitoring across distributed hospitality infrastructure.
Powered by S3M Security Platform
Hospitality cybersecurity architecture must function as a continuous identity-driven control plane across guest networks,
operational systems, and venue infrastructure.
How Security Architecture Operates Across
Hospitality Environments
Hospitality environments operate under continuously changing operational conditions. Hotels, resorts, stadiums, and conference venues must support thousands of guest devices, operational systems, and temporary infrastructure connections every day.
Traditional security models struggle to maintain visibility and control in these highly dynamic environments.
The following scenarios illustrate how identity-driven security architecture protects hospitality infrastructure while maintaining seamless connectivity for guests, staff, and operational systems.
Guest WiFi Infrastructure Access
Scenario
Threat
Architectural Response
Operational Impact
Smart Room IoT Device Connectivity
Scenario
Threat
Architectural Response
Operational Impact
Conference and Event Network Access
Scenario
Threat
Architectural Response
Operational Impact
Payment and POS Network Protection
Scenario
Threat
Architectural Response
Operational Impact
Multi-Property Network Governance
Scenario
Threat
Architectural Response
Operational Impact
Hospitality organizations require cybersecurity architectures capable of protecting operational infrastructure while supporting open connectivity environments. Identity-driven security enforcement enables hospitality operators to secure guest networks, IoT systems, and venue infrastructure without disrupting the guest experience.
Operational Security Use Cases
Modern smart cities rely on highly connected digital ecosystems that integrate public services, critical infrastructure, IoT networks, and large-scale connectivity platforms. As these environments expand, securing device identity, network access, and operational communication becomes essential to maintaining resilient urban infrastructure.
The following operational security use cases demonstrate how identity-driven access control, device profiling, and network segmentation enforce security across distributed city networks. Each scenario illustrates how S3M Security transforms large-scale connectivity into a controlled and verifiable security architecture.
Public Connectivity Infrastructure
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Unmanaged Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Guest Network Isolation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Remote Workforce
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Vendor Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Through identity-aware network enforcement, municipalities and smart city operators gain the ability to control how devices, users, and infrastructure systems interact across the urban environment. By combining visibility, segmentation, and secure connectivity, S3M Security enables cities to scale digital services while maintaining operational resilience and infrastructure-level security.
Identity-Driven Security Architecture for Hospitality & Large Venue Networks
Hotels, resorts, stadiums, and large entertainment venues operate complex digital environments where guest connectivity, operational networks, IoT systems, and service platforms continuously interact. Securing these environments requires a unified architecture capable of controlling device access, segmenting networks, and enforcing security policies across highly dynamic infrastructures.
S3M Security provides an identity-driven network security architecture designed specifically for environments with high device density, transient users, and distributed infrastructure. Each platform component contributes to a layered security model that protects guest services, operational systems, and connected devices without disrupting the guest experience.
Role Description
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
Together, these platform components create a unified security architecture that allows hospitality operators and venue administrators to control access, secure connected devices, and protect operational infrastructure at scale. By combining identity-aware network enforcement, secure connectivity, and infrastructure visibility, S3M Security enables venues to deliver seamless guest services while maintaining enterprise-grade cybersecurity.
Security Outcomes for Hospitality and Large Venue Infrastructure
Hospitality environments and large venues operate highly dynamic digital infrastructures where guest connectivity, operational systems, IoT devices, and service platforms interact continuously. Protecting these environments requires security architectures capable of enforcing identity-aware access policies and maintaining visibility across distributed networks.
The following strategic outcomes illustrate how S3M Security enables hospitality operators and venue administrators to transform network access into a controlled and enforceable security layer across their digital infrastructure.
Unified Security Control Plane
Secure Vendor and Partner Access
Regulatory Compliance Enablement
Operational Continuity
Secure Workforce Mobility
Scalable Security Governance
Continuous Infrastructure Visibility
Zero Trust Enforcement
Frequently Asked Questions
Can S3M help large venues manage thousands of temporary guest connections?
How does S3M protect staff and operational systems in hospitality environments?
Does deploying S3M security architecture cause downtime for hospitality operations?
How does S3M improve visibility across complex hospitality networks?
What compliance frameworks can S3M support in hospitality environments?
How can cybersecurity protect guest WiFi networks in hotels and large venues?
How does Zero Trust network security apply to hospitality infrastructure?
Can S3M integrate with existing hotel network infrastructure without replacing hardware?
How can hospitality organizations protect payment systems and POS terminals?
How are IoT devices in hotels and venues secured?
Design a Secure Digital Infrastructure for Hospitality and Large Venues
Hospitality environments and large public venues rely on highly connected infrastructures that support guest services, operational systems, and thousands of unmanaged devices. Securing these environments requires a unified architecture capable of enforcing identity-based access control, protecting connected devices, and maintaining visibility across distributed networks.
S3M Security works with hospitality operators, resorts, stadiums, and large venue organizations to design scalable security architectures that protect digital infrastructure without disrupting the guest experience.
