LAW ENFORCEMENT & PUBLIC SAFETY
Law Enforcement Cybersecurity Architecture
Law enforcement agencies operate some of the most sensitive digital infrastructures within government environments. Patrol vehicles access criminal justice databases in real time, emergency command centers coordinate incident response, and investigative teams rely on secure digital evidence systems.
As policing becomes increasingly data-driven, protecting these systems requires identity-driven cybersecurity architecture. S3M Security enables police organizations to secure distributed networks, patrol units, and investigative systems using Zero Trust principles designed for modern public safety operations.
The Cyber Risk Landscape Facing Law Enforcement
Modern law enforcement agencies operate highly distributed digital infrastructures. Police stations, patrol vehicles, forensic systems, and emergency command centers must exchange critical operational data in real time.
This interconnected environment expands the cyber attack surface significantly. Criminal organizations, nation-state actors, and cybercriminal groups increasingly target public safety infrastructure to disrupt investigations, steal sensitive intelligence, or disable emergency response systems.
Without identity-driven cybersecurity architecture, traditional network controls struggle to protect law enforcement infrastructure against modern threats.

Distributed Police Infrastructure
Law enforcement networks extend across precincts, patrol vehicles, mobile devices, and emergency response centers. Each connection point increases exposure to cyber threats and unauthorized access.
Sensitive Criminal Justice Data
Police databases contain criminal records, investigative intelligence, and digital evidence. Unauthorized access or data manipulation can compromise investigations and legal proceedings.
Mobile Patrol Connectivity
Patrol vehicles rely on secure connectivity to access license plate recognition systems, criminal databases, and command center coordination platforms during active operations.
Ransomware Targeting Public Agencies
Government and public safety organizations increasingly face ransomware attacks aimed at disrupting emergency services and critical public infrastructure.
Modern law enforcement infrastructure can no longer rely on perimeter-based security assumptions. Police networks now extend across patrol vehicles, precinct systems, mobile devices, and distributed operational environments.
In this highly connected ecosystem, every device, user, and network interaction becomes a potential entry point for cyber threats. Without continuous identity validation and architectural security enforcement, traditional security controls struggle to protect investigative systems, criminal justice databases, and emergency response operations.
This shift is forcing law enforcement organizations to rethink how cybersecurity is implemented — moving from isolated security tools toward identity-driven security architecture designed for distributed public safety networks.
Why Traditional Network Security Fails
in Law Enforcement Environments
Traditional cybersecurity models were designed for centralized corporate networks where users and systems operated inside clearly defined internal boundaries. In law enforcement environments, those assumptions no longer apply.
Police operations now span patrol vehicles, remote command centers, mobile devices, and distributed precinct networks. Officers must access criminal justice systems from the field while investigative teams work across multiple facilities and agencies.
In this operational model, perimeter-based security tools alone cannot provide sufficient protection. Once access is granted to a network, traditional systems often assume internal trust — allowing compromised devices or unauthorized users to move laterally across critical infrastructure.
As a result, many law enforcement organizations remain exposed to cyber threats despite deploying conventional firewalls and network segmentation controls.
Modern policing requires real-time access to sensitive systems from multiple operational environments. Patrol units, digital investigation teams, forensic labs, and emergency response centers must all connect securely to shared infrastructure.
However, traditional network security architectures were never designed for this level of operational mobility. Static VLAN segmentation, perimeter firewalls, and implicit trust models struggle to protect dynamic, distributed public safety environments.
Without continuous identity validation and device posture verification, attackers can exploit a single compromised endpoint to gain access to investigative systems, evidence repositories, or command infrastructure.
This structural weakness makes legacy security approaches increasingly ineffective against modern cyber threats targeting law enforcement agencies.
As policing infrastructure becomes increasingly distributed and data-driven, cybersecurity must evolve beyond perimeter defenses. Protecting modern law enforcement networks requires continuous identity verification, device trust enforcement, and centralized visibility across the entire operational environment.
This shift is driving public safety organizations toward Zero Trust security architecture designed specifically for distributed police infrastructure.
Key Structural Weaknesses in Traditional Security Models
- Implicit Network Trust
Traditional security assumes internal traffic is safe once access is granted.
- Limited Device Visibility
Security teams often lack full visibility across patrol devices and field terminals.
- Static Segmentation
Legacy VLAN segmentation cannot dynamically enforce identity-based access control.
- Mobile Connectivity Exposure
Patrol units rely on external cellular networks that may introduce security risks.
A Zero Trust Security Architecture for
Law Enforcement Infrastructure
Modern law enforcement environments require security architecture that operates across distributed infrastructure. Patrol vehicles, precinct networks, investigative systems, and emergency command centers must all connect securely without slowing operational workflows.
S3M Security enables identity-driven cybersecurity architecture designed specifically for law enforcement infrastructure. By enforcing Zero Trust principles across users, devices, and networks, agencies gain continuous control over who can access critical systems and how those systems interact.
This architecture protects criminal justice databases, digital evidence platforms, and operational communication systems while maintaining the speed required for modern policing.
Identity-Based Network Access
ConnGuard NAC verifies every device connecting to police infrastructure. Unauthorized devices are automatically blocked while verified endpoints receive role-based access to investigative systems.
Endpoint Threat Protection
EndGuard EPP continuously monitors investigative workstations and command center systems to detect ransomware, malware, or suspicious device activity across law enforcement networks.
Secure Public Connectivity
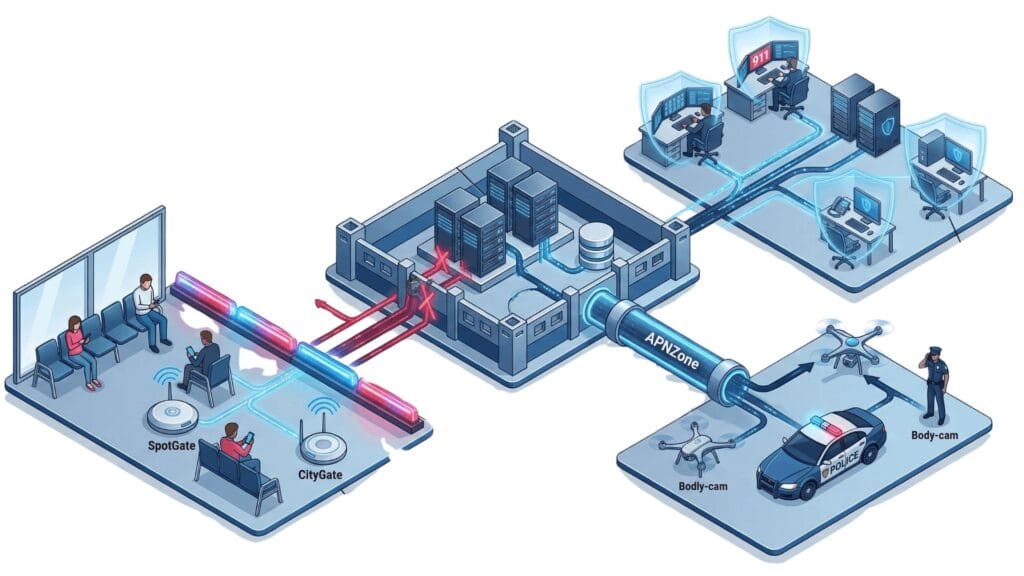
SpotGate enables police stations to provide controlled internet access for visitors while keeping operational police networks completely isolated and protected.
Encrypted Patrol Connectivity
APNZone provides secure encrypted connectivity between patrol vehicles, mobile terminals, and central command systems, protecting sensitive data transmitted across cellular networks.
Identity-driven cybersecurity architecture enables law enforcement agencies to secure distributed infrastructure without slowing operational response. By combining network access control, endpoint protection, secure connectivity, and centralized policy enforcement, S3M Security creates a resilient digital foundation for modern public safety operations.
Identity-Driven Security Architecture for
Law Enforcement Networks
Modern law enforcement infrastructure requires security architecture that validates identity across users, devices, and network environments. Patrol vehicles, precinct networks, investigative systems, and emergency command centers must all connect securely without exposing sensitive operational data.
An identity-driven Zero Trust architecture ensures that every device and user is continuously verified before accessing police infrastructure systems. This approach enables law enforcement agencies to maintain operational speed while protecting criminal justice data and investigative systems.
The architecture operates across multiple security layers. Identity verification ensures that only authorized officers and verified devices can access investigative systems and criminal justice databases. Network segmentation isolates sensitive infrastructure such as digital evidence platforms and intelligence systems.
Encrypted communication protects data transmitted between patrol units and central command systems, while centralized policy enforcement provides visibility across distributed police infrastructure.
This layered security architecture allows law enforcement agencies to maintain operational agility while ensuring that sensitive investigative data remains protected.
Real-World Cybersecurity Scenarios in
Law Enforcement Operations
Modern law enforcement agencies operate across highly distributed digital environments. Patrol vehicles, precinct networks, investigative systems, and emergency command centers all depend on secure connectivity to function effectively.
These operational environments introduce unique cybersecurity challenges that traditional network security models struggle to address. From protecting criminal justice databases to securing mobile patrol connectivity, law enforcement organizations must ensure that sensitive systems remain accessible only to verified users and trusted devices.
The following scenarios illustrate how identity-driven security architecture enables police departments and public safety organizations to protect operational infrastructure while maintaining the speed and reliability required for real-time response.
Secure Patrol Vehicle Connectivity
Scenario
Threat
Architectural Response
Operational Impact
Criminal Justice Database Protection
Scenario
Threat
Architectural Response
Operational Impact
Emergency Command Center Security
Scenario
Threat
Architectural Response
Operational Impact
Secure Guest Access in Police Facilities
Scenario
Threat
Architectural Response
Operational Impact
As law enforcement operations become increasingly digital and interconnected, cybersecurity must evolve beyond perimeter defenses and isolated security tools. Protecting investigative systems and public safety infrastructure requires architecture that continuously verifies identity, enforces device trust, and maintains visibility across distributed operational environments.
By implementing identity-driven Zero Trust architecture, law enforcement agencies can secure patrol connectivity, investigative platforms, and command infrastructure while enabling officers and analysts to access the systems they need without operational delays.
Operational Security Use Cases for
Law Enforcement & Public Safety
Law enforcement agencies operate highly distributed digital environments that connect patrol vehicles, command centers, investigation systems, and field personnel.
These interconnected systems must provide real-time access to sensitive databases while maintaining strict security controls and regulatory compliance.
The following operational use cases demonstrate how identity-driven access control, encrypted connectivity, and network segmentation protect law enforcement infrastructure while ensuring uninterrupted operational response.
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Critical Infrastructure Segmentation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Identity-driven network control enables law enforcement agencies to protect sensitive investigative systems while maintaining secure, real-time connectivity for field operations.
Core Security Components Powering Law Enforcement Infrastructure
odern law enforcement environments rely on interconnected
Role Description
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
EndGuard evaluates device posture across traffic sensors, municipal workstations, and IoT endpoints embedded throughout city infrastructure. Trust is not static; it is continuously reassessed based on behavioral indicators and compliance posture.
In smart city environments where thousands of connected devices operate simultaneously, compromised endpoints can quickly become lateral access vectors. Posture-aware enforcement limits exposure while maintaining operational continuity.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
Together, these security components form a unified architecture that protects law enforcement infrastructure from unauthorized access, device compromise, and lateral movement while ensuring that officers, investigators, and command personnel maintain secure and reliable access to the systems they depend on.
Strategic Security Outcomes for
Law Enforcement Organizations
Law enforcement agencies must balance operational speed with strict protection of investigative systems, criminal justice databases, and public safety infrastructure. As policing operations become increasingly digital and interconnected, security architecture must evolve to provide continuous visibility, identity-driven control, and resilient infrastructure protection.
A unified cybersecurity architecture enables agencies to secure critical systems, reduce operational risk, and maintain uninterrupted public safety services while protecting sensitive investigative data.
Unified Security Control Plane
Secure Vendor and Partner Access
Operational Continuity
Secure Workforce Mobility
By implementing identity-driven security architecture, law enforcement organizations gain stronger operational resilience, improved infrastructure visibility, and the ability to protect mission-critical systems without slowing investigative and emergency response operations.
Cybersecurity Questions Law Enforcement Agencies Ask Most
Law enforcement organizations manage highly sensitive investigative data, operational systems, and distributed infrastructure that must remain secure at all times.
Protecting criminal justice databases, patrol connectivity, and command center systems introduces cybersecurity challenges that traditional network security models cannot address.
The following questions highlight common concerns public safety agencies have when evaluating identity-driven security architecture and Zero Trust access strategies.
Why is device visibility critical in public safety networks?
How can law enforcement agencies prevent lateral movement during cyberattacks?
How can public safety organizations protect surveillance and monitoring systems?
How can security teams manage cybersecurity across multiple police departments and facilities?
What are the benefits of unified network security for law enforcement operations?
How can law enforcement agencies secure criminal databases and investigation systems?
Why is network segmentation important for police and public safety networks?
How can police departments secure mobile devices used by officers in the field?
How does Network Access Control improve security in public safety environments?
How can law enforcement agencies secure remote access for investigators and analysts?
Understanding how modern cybersecurity architecture protects investigative systems, operational networks, and public safety infrastructure helps law enforcement agencies make informed decisions about securing their digital environments.
Design a Secure Architecture for Law Enforcement Infrastructure
Law enforcement organizations operate mission-critical systems that support patrol operations, investigative platforms, emergency response coordination, and criminal justice databases. Securing these environments requires an architecture that continuously verifies identities, protects sensitive operational data, and maintains uninterrupted connectivity across distributed infrastructure.
S3M Security helps law enforcement and public safety agencies design identity-driven security architectures that protect critical systems, secure field connectivity, and ensure resilient infrastructure for modern policing operations.
Work with S3M Security experts to design a cybersecurity architecture tailored for law enforcement environments—protecting investigative systems, securing operational networks, and enabling trusted connectivity across public safety infrastructure.
