Remote access is essential for modern IT operations, but traditional tools introduce security risks, increase operational complexity, and limit visibility.
S3M Secure Remote Access eliminates third-party dependencies by providing a native, agent-based access model with encrypted connections, centralized control, and full auditability.
With the rapid adoption of hybrid work models, IT and security teams face critical risks when accessing endpoints remotely.
Third-party remote access tools such as TeamViewer and AnyDesk create uncontrolled tunnels within corporate networks, significantly expanding the attack surface. Each additional tool introduces patching, configuration, and management overhead.
Moreover, remote sessions established through these tools are not fully integrated into centralized logging systems, making it difficult to meet compliance requirements such as GDPR, ISO 27001, and SOC 2.
Switching between multiple tools for remote access, file transfer, and network control slows down operations and negatively impacts incident response times (MTTR).
S3M Secure Remote Access delivers a native, agent-based remote access capability built directly on the EndGuard Agent infrastructure.
Without requiring any additional software or licensing, IT and security teams can instantly connect to any endpoint through a single click. All remote sessions are established through encrypted tunnels and monitored in real time via the centralized S3M management console.
By eliminating third-party tools, organizations remove security blind spots and regain full control over remote access operations.
During active sessions, secure file transfer allows direct deployment of MSI packages, updates, and configuration files to target endpoints, enabling immediate intervention without physical access.
Core capabilities and strategic advantages that enable secure, controlled, and fully auditable remote access operations.
Real-world scenarios demonstrating how secure remote access is implemented for IT operations, incident response, and distributed workforce support.
Measurable business outcomes achieved through eliminating third-party tools and enforcing secure, centralized remote access control.
Industries where secure, controlled, and compliant remote access is critical for operational continuity and security.
Core platform components and technologies that power and extend the Secure Remote Access solution.
EndGuard evaluates device posture across traffic sensors, municipal workstations, and IoT endpoints embedded throughout city infrastructure. Trust is not static; it is continuously reassessed based on behavioral indicators and compliance posture.
In smart city environments where thousands of connected devices operate simultaneously, compromised endpoints can quickly become lateral access vectors. Posture-aware enforcement limits exposure while maintaining operational continuity.
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
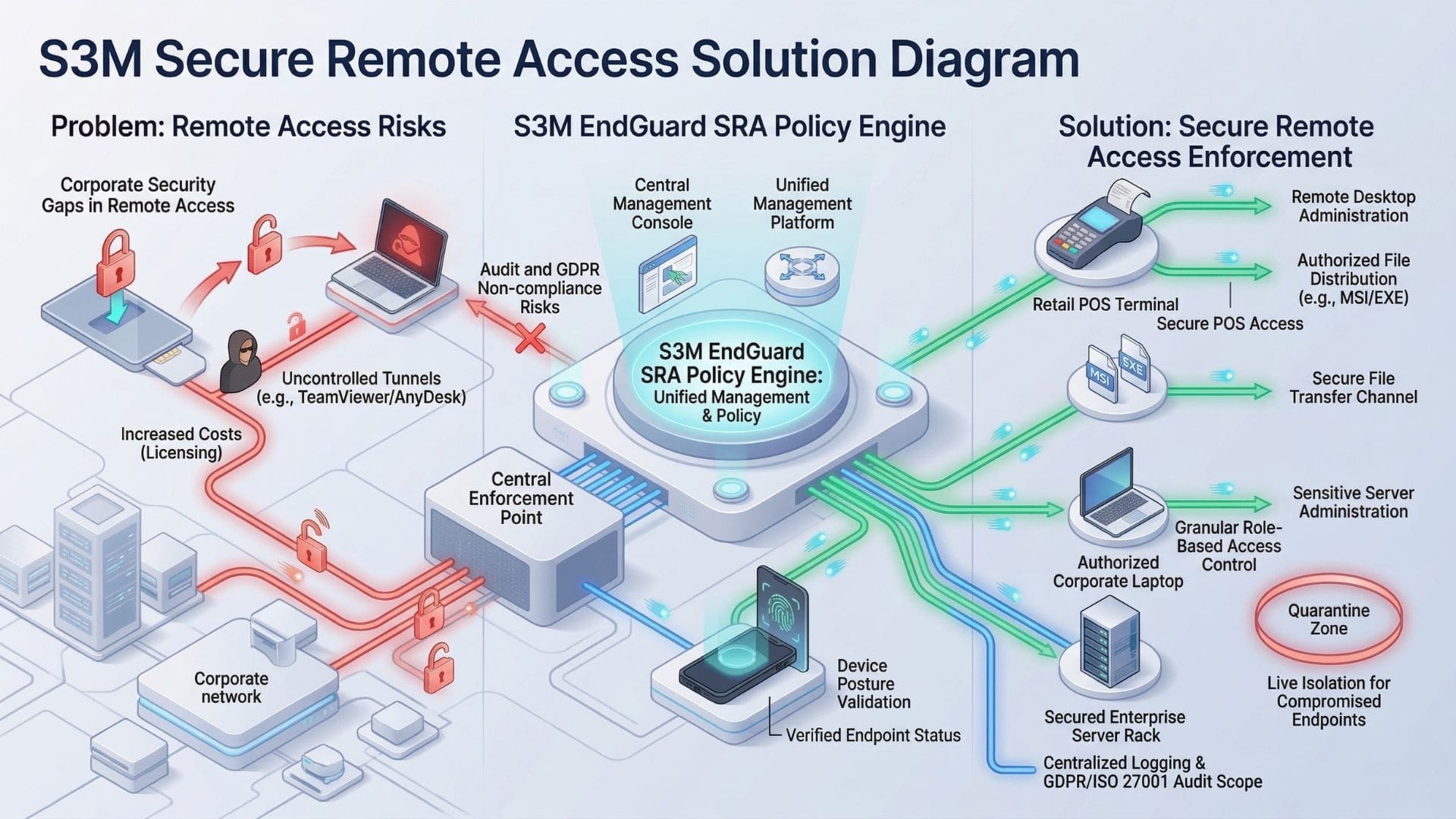
S3M Secure Remote Access is built on the EndGuard Agent deployed across enterprise endpoints.
When a remote session is initiated, the agent establishes an encrypted, end-to-end tunnel directly between the endpoint and the S3M central management console, without requiring VPN or third-party software.
All session activities, including user actions and file transfers, are monitored in real time and recorded within centralized logging systems.
Access is enforced through role-based policies and NAC integration, ensuring that every connection is controlled, auditable, and compliant with enterprise security standards.