Organizations lack visibility into which applications are running across their endpoints, creating significant security risks and operational blind spots.
S3M Application Control provides full application visibility and enforces execution policies through a native agent-based architecture.
Enterprise environments often lack visibility and control over applications running on endpoints.
Unauthorized or unknown applications are one of the most common entry points for ransomware and advanced threats. A single unapproved application can compromise the entire network.
Additionally, static security policies fail to adapt to dynamic environments where users operate across multiple locations with varying security requirements.
S3M Application Control is a comprehensive solution built on the EndGuard Agent that automatically discovers all executable applications across endpoints and creates a centralized software inventory.
Security teams can enforce application policies using whitelist or blacklist modes, controlling exactly which applications are allowed to run.
With location-based policy enforcement and NAC integration, unauthorized applications can be automatically detected and isolated in real time.
Core capabilities that provide full visibility and control over endpoint application execution.
Real-world scenarios demonstrating how application control enforces security across dynamic environments.
Business outcomes achieved through controlling application execution and eliminating unauthorized software.
Industries where application visibility and execution control are critical for security and compliance.
Core technologies that enable and extend application control capabilities across endpoints and networks.
EndGuard evaluates device posture across traffic sensors, municipal workstations, and IoT endpoints embedded throughout city infrastructure. Trust is not static; it is continuously reassessed based on behavioral indicators and compliance posture.
In smart city environments where thousands of connected devices operate simultaneously, compromised endpoints can quickly become lateral access vectors. Posture-aware enforcement limits exposure while maintaining operational continuity.
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
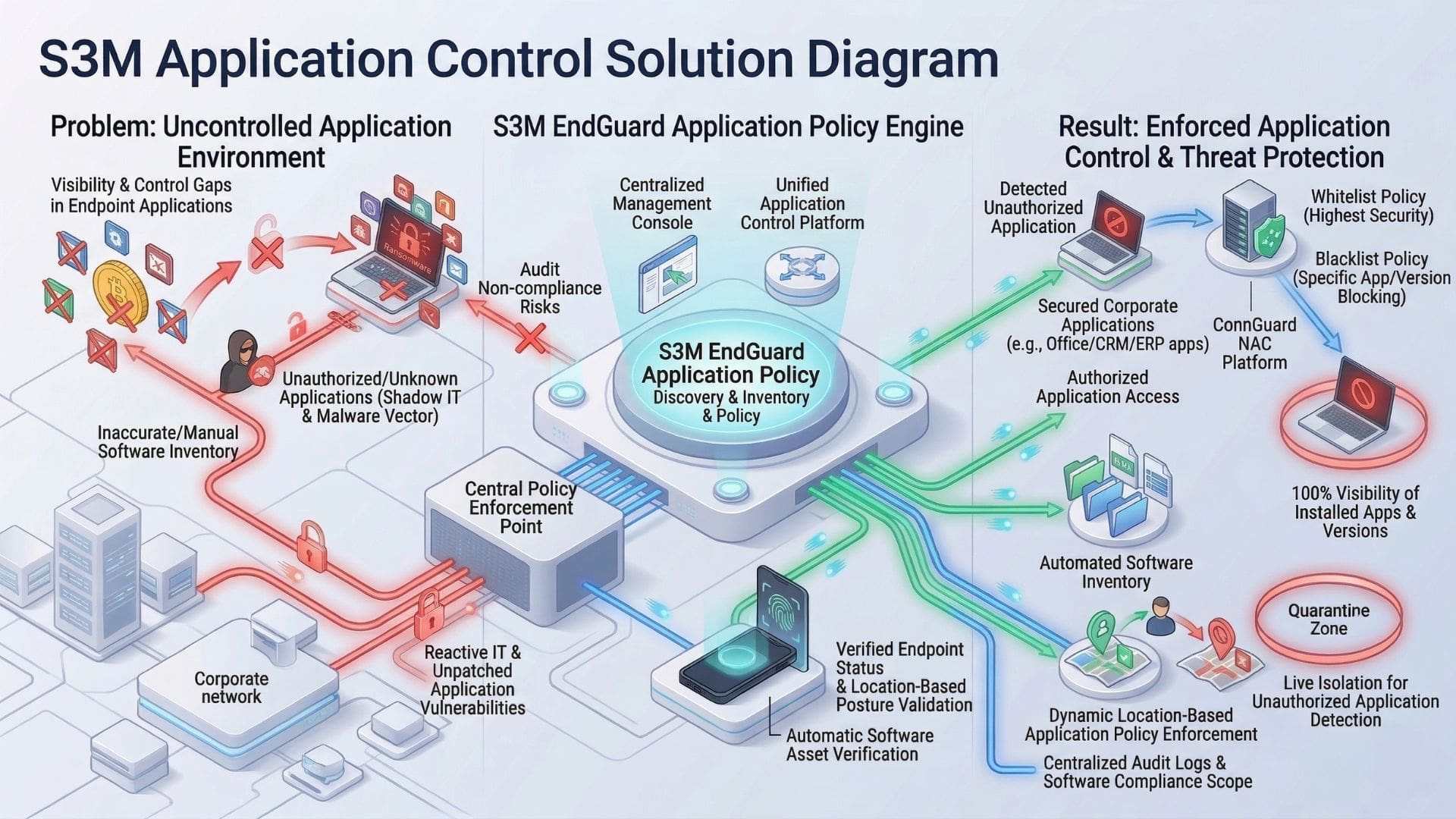
S3M Application Control operates through the EndGuard Agent deployed on endpoints.
The agent continuously monitors and reports application activity to the central management console.
When unauthorized applications are detected, policies are enforced instantly, and NAC integration enables automatic network isolation of affected endpoints.