NETWORK SECURITY FOR TELECOMMUNICATIONS
Telecommunications & ISPs Network Security Architecture
Identity-Driven Security for Carrier Infrastructure and ISP Networks
Telecommunications operators and Internet service providers manage vast digital infrastructures spanning fiber backbones, mobile networks, and distributed data centers.
Traditional perimeter security cannot protect these highly distributed environments.
S3M Security delivers an identity-driven telecommunications network security architecture that enforces Zero Trust controls across users, devices, and network sessions — enabling telecom providers to secure infrastructure, subscriber services, and operational systems without disrupting service delivery.
The Expanding Cyber Risk Landscape for Telecommunications Networks
Telecommunications networks are no longer centralized infrastructure systems. Modern operators manage distributed environments that include fiber backbone networks, 5G access layers, carrier data centers, edge nodes, and millions of subscriber devices connecting every day.
This scale of connectivity has fundamentally expanded the cyber attack surface facing telecom providers.
Subscriber devices, IoT endpoints, roaming connections, and distributed infrastructure all interact within the same network ecosystem. Without identity-driven visibility and control, telecom security teams often lack real-time awareness of which users, devices, or systems are interacting across network segments.
As telecom networks evolve into highly distributed digital platforms, traditional perimeter-based protection becomes increasingly ineffective.
Key structural risks facing telecommunications infrastructure include:
- Millions of unmanaged subscriber devices connecting to carrier networksmedical devices connected to clinical networks
- Distributed edge infrastructure across regional telecom sites
- Lateral exposure between operational systems and subscriber services
- Increasing regulatory pressure on telecom data protection and logging
- Limited real-time visibility across subscriber sessions and infrastructure layers
- Expanding attack surface across 5G, IoT, and edge network environments
Telecommunications security must therefore evolve beyond perimeter defense toward identity-driven network security architecture capable of protecting distributed carrier infrastructure at scale.
Why Telecom Security Architectures Fail
— Even When Everything Looks Protected
Most telecom security failures do not happen because systems are unprotected.
They happen because security architectures were designed for the wrong network model.
Traditional enterprise security assumes a stable environment:
known users, fixed infrastructure, and predictable network boundaries.
Telecommunications networks operate under the exact opposite conditions.
Telecom operators manage infrastructure where millions of identities interact with distributed systems simultaneously.
Subscribers move across networks.
Devices continuously reconnect through new access points.
Operational systems interact across infrastructure layers.
Under these conditions, legacy security assumptions begin to collapse.
Firewall-Centric Security
Firewalls protect boundaries.
Telecom networks rarely have clear boundaries.
Subscriber sessions originate from mobile networks, roaming partners, public internet access, and distributed edge infrastructure.
Security cannot rely on perimeter inspection when the perimeter itself no longer exists.
Static Network Segmentation
Traditional segmentation divides infrastructure by department or network zone.
Telecommunications environments operate across operational systems, subscriber platforms, and distributed infrastructure layers.
Without identity-aware segmentation, attackers can move laterally across systems that were never designed to trust each other.
IP-Based Policy Models
IP addresses once represented identity.
In telecom infrastructure they represent temporary routing states.
Mobile devices change networks constantly, edge nodes dynamically allocate addresses, and subscriber sessions shift across access technologies.
Security policies tied to IP addresses lose their meaning in such environments.
Manual Security Operations
Legacy security processes rely heavily on manual approvals, onboarding workflows, and fragmented policy management.
Telecommunications infrastructure requires automation.
Carrier environments demand policy enforcement capable of operating across millions of sessions simultaneously without introducing operational friction.
The fundamental challenge is not deploying more security tools.
It is building a telecommunications network security architecture capable of enforcing identity, context, and policy across distributed carrier infrastructure.
SECURITY ARCHITECTURe
Identity-Driven Security Architecture for Telecom Infrastructure
Telecommunications networks operate across national backbone infrastructure, mobile access networks, distributed edge nodes, and carrier data centers. These environments require security architecture capable of protecting infrastructure without introducing operational latency or service disruption.
Traditional perimeter defenses cannot enforce security across such distributed infrastructure layers.
- Identity-based network access enforcement
- Continuous device posture validation
- Dynamic micro-segmentation across telecom infrastructure
- Secure orchestration across carrier data centers and edge nodes
- Real-time visibility across subscriber sessions and network services

S3M Security implements an identity-driven telecommunications network security architecture that applies Zero Trust principles across users, devices, and infrastructure systems. Instead of relying on network location, access decisions are enforced based on identity, device posture, and operational context.
This approach transforms telecom security from isolated control points into a continuous architectural control layer operating across the entire carrier network.
Telecommunications security must function as a network architecture layer — not a perimeter defense tool.
Zero Trust Architecture for Telecommunications Networks
Telecommunications infrastructure operates across multiple security domains simultaneously. Subscriber connectivity, operational systems, network management platforms, and distributed infrastructure must all interact without exposing critical systems to unauthorized access.
A Zero Trust telecommunications network security architecture ensures that every user, device, and network session is authenticated, validated, and continuously monitored before gaining access to infrastructure services.
Security therefore operates as a control layer across the entire telecom network, rather than a single inspection point at the perimeter.
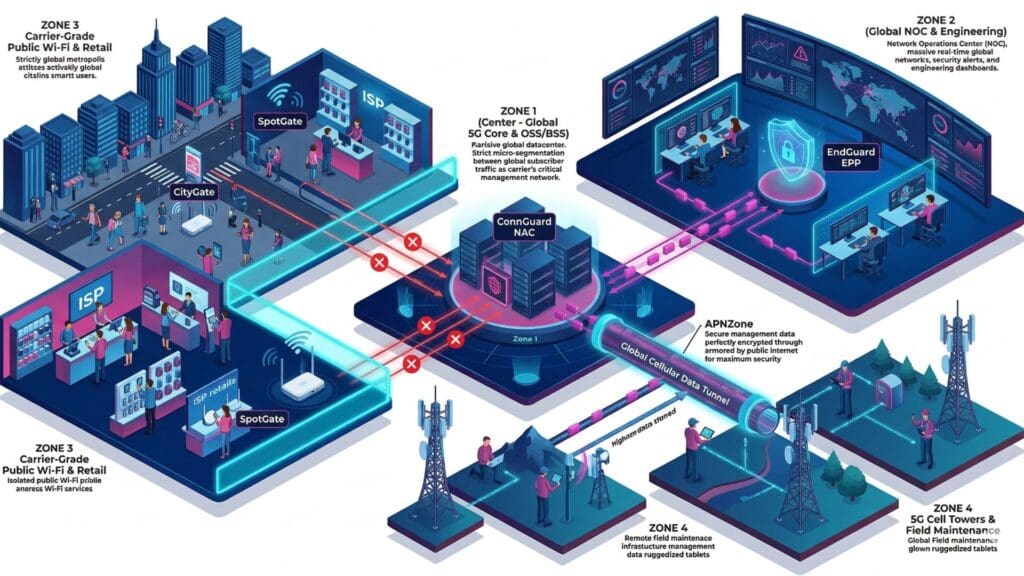
Identity Access Layer
Every connection entering telecom infrastructure must first establish identity. Subscribers, internal users, operational systems, and connected devices are authenticated before network sessions are established.
Access decisions follow verified identity rather than network location.
Device & Endpoint Posture Layer
Devices connecting to telecom networks are evaluated based on security posture, behavioral indicators, and operational context. Devices that fail compliance checks can be restricted or isolated automatically.
This ensures compromised devices cannot access sensitive network services.
Network Segmentation Layer
Dynamic micro-segmentation prevents lateral movement across telecom infrastructure. Subscriber networks, operational systems, and network management platforms remain logically isolated.
Only explicitly authorized communication paths are allowed.
Infrastructure Protection Layer
Carrier infrastructure including edge nodes, backbone networks, and data centers operates within controlled security zones. Communications between infrastructure components occur through encrypted and policy-controlled channels.
Centralized Security Orchestration
Security policies are orchestrated centrally and enforced across telecom infrastructure in real time. This enables consistent policy enforcement across distributed carrier networks, cloud platforms, and operational systems.
Telecommunications infrastructure can no longer rely on perimeter-based protection. Carrier networks require identity-driven security architecture capable of enforcing policy across millions of distributed connections in real time.
Zero Trust transforms telecom cybersecurity from reactive protection into a structural component of network architecture.
Real-World Cybersecurity Scenarios in Telecommunications Networks
Telecommunications infrastructure operates at national and global scale, supporting millions of subscribers, distributed network nodes, and complex service platforms. Within such environments, even small security gaps can create cascading operational risks affecting network availability, data integrity, and subscriber trust.
Cyber threats targeting telecom operators increasingly focus on infrastructure layers such as authentication systems, network orchestration platforms, edge computing nodes, and core routing environments. These attacks are rarely isolated incidents; they often attempt to exploit the interconnected nature of telecom infrastructure to move laterally across systems.
The following scenarios illustrate how modern telecommunications security architecture can identify, contain, and prevent threats before they disrupt critical connectivity services or expose sensitive infrastructure.
Edge Network Infrastructure Security
Scenario
Threat
Architectural Response
Operational Impact
ISP Broadband Access Security
Scenario
Threat
Architectural Response
Operational Impact
Secure Subscriber Authentication Systems
Scenario
Threat
Architectural Response
Operational Impact
5G Core Network Access Protection
Scenario
Threat
Architectural Response
Operational Impact
By applying identity-driven controls and Zero Trust principles across telecom infrastructure, operators gain the ability to detect abnormal behavior, restrict unauthorized access, and isolate compromised systems before they impact network operations or subscriber services.
Operational Security Use Cases for Telecom Infrastructure
Telecommunications networks operate as highly dynamic environments where millions of users, devices, and infrastructure components interact simultaneously. Security architecture must therefore function continuously across operational processes rather than relying on isolated protection points.
Identity-driven network security enables telecom operators to enforce access control, device validation, and segmentation across the entire infrastructure lifecycle. From subscriber authentication to infrastructure management and distributed edge services, security policies operate in real time to prevent unauthorized access and lateral movement.
These operational use cases demonstrate how telecommunications providers can protect carrier infrastructure while maintaining the performance, scalability, and availability required for modern connectivity services.
Critical Infrastructure Segmentation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
By embedding security controls directly into telecom network operations, operators transform cybersecurity from a reactive defense mechanism into a continuous operational capability. Identity-driven architecture ensures that every connection — whether originating from subscribers, infrastructure systems, or operational teams — is verified, controlled, and monitored across the entire telecommunications environment.
Security Architecture Layers for Telecommunications Networks
Telecommunications infrastructure requires multiple security layers operating simultaneously across subscriber access, network infrastructure, and operational systems. Rather than relying on isolated tools, modern telecom cybersecurity must function as an integrated architecture that enforces identity verification, device control, and network segmentation across distributed carrier environments.
S3M Security delivers this architecture through specialized security components designed to protect telecom networks without disrupting service performance or operational workflows.
Role Description
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
Role Description
SpotGate manages structured onboarding and lawful logging across public WiFi deployments. Guest traffic is authenticated, logged, and structurally segmented from operational municipal systems.
In city-wide deployments — including WiFi4EU environments — public access must remain citizen-friendly while maintaining strict architectural separation from internal networks.
Role Description
EndGuard evaluates device posture across traffic sensors, municipal workstations, and IoT endpoints embedded throughout city infrastructure. Trust is not static; it is continuously reassessed based on behavioral indicators and compliance posture.
In smart city environments where thousands of connected devices operate simultaneously, compromised endpoints can quickly become lateral access vectors. Posture-aware enforcement limits exposure while maintaining operational continuity.
Role Description
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
Together, these architecture layers create a carrier-grade telecommunications network security architecture capable of protecting subscriber services, operational infrastructure, and distributed network environments without disrupting service delivery.
By combining identity-based access control, endpoint protection, secure connectivity, and network isolation, S3M Security enables telecom operators to enforce Zero Trust security principles across the entire telecommunications ecosystem.
Strategic Security Outcomes for Telecommunications Operators
Telecommunications providers operate some of the most critical infrastructure in the digital economy. As networks expand to support 5G, fiber connectivity, edge computing, and large-scale IoT ecosystems, security must evolve beyond isolated tools toward a unified operational strategy.
By implementing identity-driven network access controls, infrastructure visibility, and centralized policy enforcement, telecom operators can reduce cyber risk while maintaining the performance and reliability expected from carrier-grade networks.
S3M Security enables telecommunications organizations to transform network security into a strategic capability — protecting infrastructure, ensuring service continuity, and enabling secure digital growth across distributed telecom environments.
Unified Security Control Plane
Secure Vendor and Partner Access
Operational Continuity
Scalable Security Governance
For telecommunications providers, cybersecurity is no longer just an IT concern — it is a core operational requirement. A unified security architecture allows operators to maintain network integrity, protect subscriber services, and securely scale infrastructure as demand continues to grow.
With the right architecture in place, telecom organizations can shift from reactive security operations to proactive infrastructure protection across their entire network ecosystem.
Telecommunications Cybersecurity FAQs
Telecommunications networks operate at a scale few industries experience. Millions of subscriber devices, distributed infrastructure components, and continuous network traffic create a highly complex security environment.
As telecom providers expand 5G infrastructure, fiber networks, and edge computing environments, security teams must address new risks related to device authentication, infrastructure visibility, and third-party access.
The following frequently asked questions explain how modern cybersecurity architecture helps telecommunications operators secure network infrastructure, protect subscriber services, and maintain operational continuity across large-scale telecom environments.
Why do telecommunications networks require Zero Trust security architecture?
How can telecom operators secure millions of subscriber devices?
How does S3M help telecom providers secure network infrastructure?
Can S3M integrate with existing telecom network equipment?
How are telecom field engineers and remote teams securely connected?
How can telecom providers monitor network devices and connections in real time?
How does S3M help telecom operators maintain service continuity?
Can telecom operators control third-party vendor access to network systems?
How does S3M support regulatory compliance in telecommunications?
Why is network segmentation important for telecom infrastructure security?
Telecommunications cybersecurity requires a proactive, architecture-driven approach that combines identity-based access control, infrastructure visibility, and continuous monitoring.
With the right security architecture in place, telecom providers can protect critical infrastructure, maintain service reliability, and safely support the growing demand for high-speed digital connectivity.
