Energy Infrastructure Cybersecurity
Secure Energy Infrastructure with Identity-Driven Zero Trust
Protecting Smart Grids, SCADA Systems and Distributed Energy Networks
Modern energy infrastructure is no longer centralized.
It operates across power plants, substations, renewable energy sites and remote field assets — all connected through complex IT and OT networks.
This distributed architecture creates critical visibility gaps and exposes operational systems to advanced cyber threats.
S3M delivers an identity-enforced Zero Trust architecture designed specifically for energy environments — securing SCADA, ICS and grid infrastructure without disrupting operations.
Energy Threat Landscape
The Expanding Cyber Risk Across Energy Infrastructure
Energy infrastructure is rapidly transforming into a highly distributed, cyber-physical ecosystem.
From centralized control rooms to remote renewable assets, every layer is now interconnected — and exposed.
However, most security architectures were never designed for this level of operational complexity.
As IT and OT environments converge, traditional visibility disappears.
Security teams lose control over who is accessing what, from where, and under which conditions — creating a perfect environment for lateral movement and targeted attacks.
Unmanaged OT & ICS Devices
Thousands of PLCs, RTUs and industrial sensors operate without embedded security, creating invisible entry points across the grid.
Remote & Untrusted Connectivity
Substations, wind farms and field assets rely on external networks, increasing exposure to interception and unauthorized access.
IT–OT Convergence Risks
Bridging corporate IT with operational systems expands the attack surface and enables lateral movement into critical infrastructure.
Lack of Real-Time Visibility
Security teams cannot see or control device identity, posture or behavior across distributed environments.
Regulatory Pressure Escalation
Standards like IEC 62443 and NERC CIP require strict segmentation, traceability and access control across energy systems.
Nation-State Threat Exposure
Energy infrastructure is a primary target for advanced persistent threats (APT) and geopolitical cyber operations.
Energy infrastructure can no longer rely on implicit trust between systems.
Security must shift from network-based assumptions to identity-driven control across every connection, device and access point.
Security Model Breakdown
Why Traditional Energy Security Models Fail
Energy infrastructure was never designed for today’s distributed, interconnected and identity-less environments.
Traditional security models assume control over network boundaries —
but in energy systems, those boundaries no longer exist.
As field assets, SCADA systems and third-party connections expand,
security must operate continuously — not only at the perimeter.
Perimeter-Based Security
Firewalls protect edges — not distributed infrastructure.
Energy networks operate far beyond centralized boundaries.
Static Network Segmentation
VLAN-based segmentation cannot prevent lateral movement across dynamic OT environments.
IP-Based Trust Models
IP addresses do not represent identity.
Devices move, sessions change, trust assumptions break.
Manual Access Control
Human-driven approvals and static policies cannot scale across thousands of distributed assets.
The result is a structural security gap —
where access is granted without continuous verification, and threats move undetected across critical systems.
Security Architecture
Zero Trust Architecture for Energy Infrastructure
Energy infrastructure requires more than isolated security controls.
It demands a continuous, identity-driven security architecture that spans across IT, OT and field environments.
S3M establishes a unified control plane where every connection, device and user is verified, segmented and continuously monitored.
Instead of relying on network location, access decisions are enforced based on identity, device posture and operational context — eliminating implicit trust across the grid.
Identity Enforcement Layer
Every device, operator and system must be authenticated and authorized before accessing energy infrastructure.
Endpoint Protection Layer
Critical control systems and operator endpoints are continuously monitored and protected against advanced threats.
Powered By : EndGuard EPP
Secure Connectivity Layer
Remote substations, renewable assets and field systems connect through encrypted, carrier-grade private networks.
Powered By : APNZone
Access & Isolation Layer
Third-party vendors and external users are fully isolated from operational systems with controlled access policies.
Powered By : SpotGate
An Identity-Driven Security Architecture for Smart Cities
Healthcare environments require continuous identity validation across users, devices, applications, and infrastructure layers. Security must operate as an architectural control plane — not as an isolated product layer.
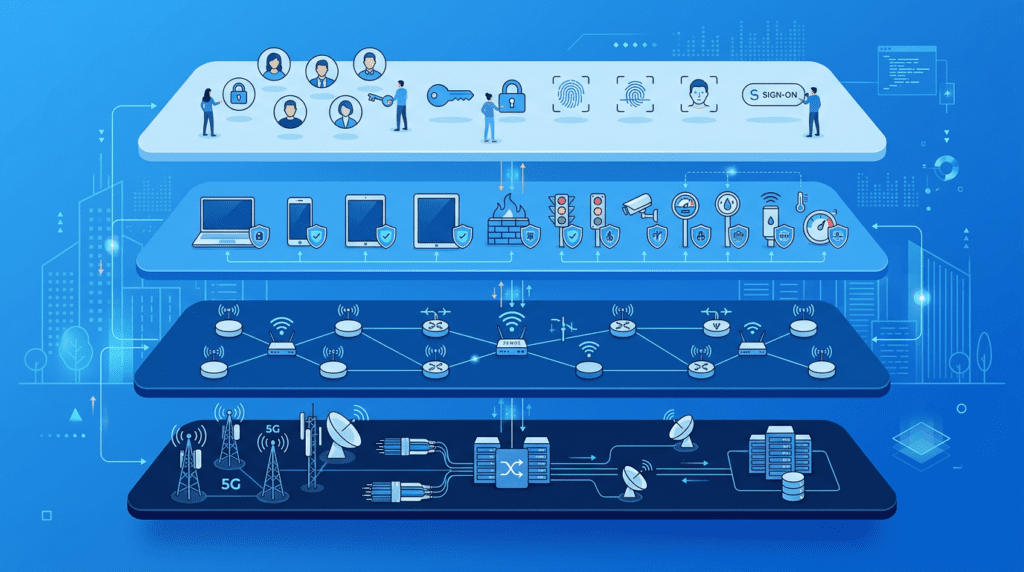
Identity Access Layer
Identity becomes the primary enforcement mechanism across smart city infrastructure. Every user, device, and service must be authenticated and continuously validated before access is granted.
Access decisions follow identity, not network location.
Endpoint & Device Posture Layer
Devices are evaluated based on compliance state, behavioral indicators, and operational context. Trust is dynamic, not permanent.
Device posture directly influences network segmentation and access privileges.
Public Connectivity Governance Layer
Public WiFi sessions are isolated, logged, and policy-controlled to prevent lateral exposure into municipal systems.
Guest access must remain auditable and structurally separated from operational infrastructure.
Mobile & Distributed Infrastructure Layer
Field assets, IoT sensors, and remote systems operate through encrypted and policy-enforced channels beyond physical network boundaries.
Security enforcement extends beyond physical perimeters into mobile and carrier environments.
Carrier-Grade Orchestration Layer
Policy decisions are synchronized across access points, districts, data centers, and cloud environments to ensure architectural consistency.
Centralized orchestration eliminates fragmented security controls across city infrastructure.
Smart city security must function as an integrated architectural model — not as fragmented point solutions layered onto legacy infrastructure.
Architecture in Action: Smart City Operational Scenarios
A layered architecture only proves its value when it operates under real-world pressure. The following scenarios illustrate how identity-driven enforcement reshapes municipal cybersecurity outcomes.
Smart city cybersecurity must function dynamically under operational pressure — not only under theoretical architectural design.
Operational Security Use Cases
The following operational security capabilities demonstrate how identity-driven access control and network segmentation protect connected urban infrastructure. Each use case illustrates how S3M Security architecture transforms city-scale connectivity into an enforceable security control layer.
Network Visibility
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Unmanaged Device Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IoT Device Security
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Remote Workforce
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Critical Infrastructure Segmentation
Scenario
Threat
Architectural Response
Operational Impact
Security Components
Secure Vendor Access
Scenario
Threat
Architectural Response
Operational Impact
Security Components
IDENTITY-DRIVEN NETWORK CONTROL ENABLES SECURE AND RESILIENT URBAN DIGITAL INFRASTRUCTURE.
Architecture Components
Supporting Smart City Security
Each architecture component contributes to enforcing identity-driven security across distributed urban infrastructure.
Role Description
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
A layered architecture only proves its value when it operates under real-world pressure. The following scenarios illustrate how identity-driven enforcement reshapes municipal cybersecurity outcomes.
Strategic Security Outcomes
Identity-driven network control enables municipalities to operate complex digital infrastructure securely while maintaining operational agility and citizen accessibility.
