Critical infrastructure systems rely heavily on cellular connectivity for SCADA operations, smart metering, and real-time telemetry.
Cellular Zero Trust Security ensures that every device, connection, and data flow is continuously verified, segmented, and controlled to prevent unauthorized access and lateral movement.
Traditional private APN architectures rely on SIM-based trust and lack identity validation, leaving critical infrastructure exposed to cellular attack vectors.
Unauthorized devices can access SCADA networks if SIM credentials are compromised, while lack of segmentation allows lateral movement between IoT devices, smart meters, and control systems.
Multi-operator environments further increase complexity, creating visibility gaps and inconsistent policy enforcement across distributed infrastructure.
Cellular Zero Trust Security transforms cellular connectivity into a fully controlled, identity-driven access model.
Each connection is validated through five independent authentication layers, including SIM identity, device binding, MAC verification, device health, and location awareness.
SCADA systems, smart meters, field devices, and IoT sensors are isolated through micro-segmentation, ensuring that each device communicates only with authorized systems.
A centralized policy engine enforces consistent security across multiple operators, while real-time policy updates allow immediate response to threats without disrupting connectivity.
Core capabilities that secure SCADA, IoT, and field devices with identity-based cellular Zero Trust enforcement.
Real-world scenarios demonstrating secure cellular connectivity across critical infrastructure environments.
Measurable business outcomes achieved through eliminating cellular attack vectors and enforcing Zero Trust security.
Industries where cellular-connected critical infrastructure requires continuous protection and control.
Core technologies that power cellular Zero Trust security across industrial and mobile environments.
APNZone secures mobile workforce connectivity across cellular networks. Field officers, maintenance teams, and emergency responders operate beyond traditional network perimeters. Encrypted private APN channels ensure that communication remains policy-enforced regardless of location.
By binding SIM identity and device validation into access control decisions, municipalities extend Zero Trust enforcement into mobile environments without sacrificing operational agility.
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
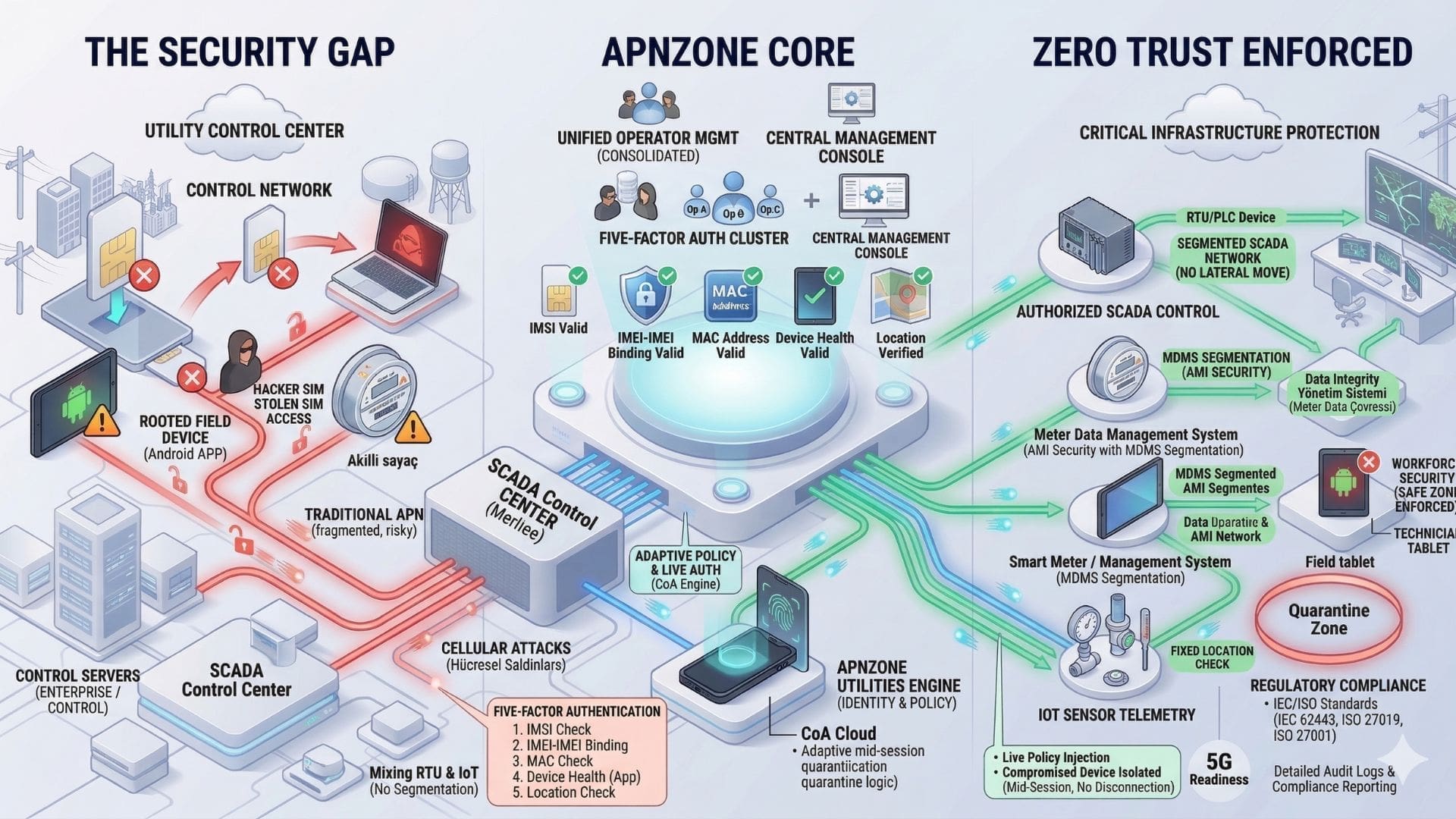
Cellular Zero Trust Security integrates APN infrastructure with a centralized policy engine to enforce identity-based access control.
Devices are validated through multiple authentication layers and segmented into isolated communication zones.
All connections are continuously monitored and controlled, ensuring secure communication across SCADA systems, IoT devices, and mobile workforce environments.