Public WiFi networks introduce significant security risks due to uncontrolled user access and lack of proper segmentation.
Public WiFi Security ensures that guest users, IoT devices, and infrastructure are isolated, authenticated, and continuously controlled through a centralized security framework.
Public WiFi environments expose organizations to unauthorized access, lateral movement, and data breaches due to weak authentication and lack of segmentation.
Traditional captive portals fail to provide strong identity validation, while distributed network environments create operational complexity and visibility gaps.
Without proper segmentation, a single compromised device can threaten the entire network.
Public WiFi Security establishes a centralized control layer that enforces identity-based access and dynamic network segmentation.
Guest users, IoT devices, and infrastructure components are continuously authenticated and assigned to isolated network segments based on policies.
The solution integrates NAC and APN technologies to provide unified control, scalability, and real-time policy enforcement across all network environments.
Core capabilities that enable secure guest access, identity-based authentication, and dynamic network segmentation across public WiFi environments.
Real-world scenarios demonstrating how public WiFi networks are secured across cities, enterprises, and high-density environments.
Measurable business outcomes achieved through secure guest access control, network isolation, and centralized policy enforcement.
Industries where secure public connectivity and controlled guest access are critical for operational continuity and user experience.
Core platform technologies that power public WiFi security, access control, and network orchestration capabilities.
CityGate synchronizes policy enforcement across districts, access points, data centers, and cloud environments. Public WiFi infrastructure operates as critical civic infrastructure, requiring telecom-grade availability and centralized control.
By clustering authentication and policy engines at scale, municipalities maintain uninterrupted connectivity while enforcing consistent Zero Trust decisions across distributed environments.
ConnGuard functions as the identity enforcement core within smart city environments. Every user, device, and system request is validated before network access is granted. Rather than relying on static VLAN structures or IP-based assumptions, policy decisions follow verified identity attributes.
In distributed municipal networks — where public WiFi users, contractors, and internal systems coexist — continuous authentication ensures that trust is dynamically reassessed. This prevents lateral movement across departments and districts.
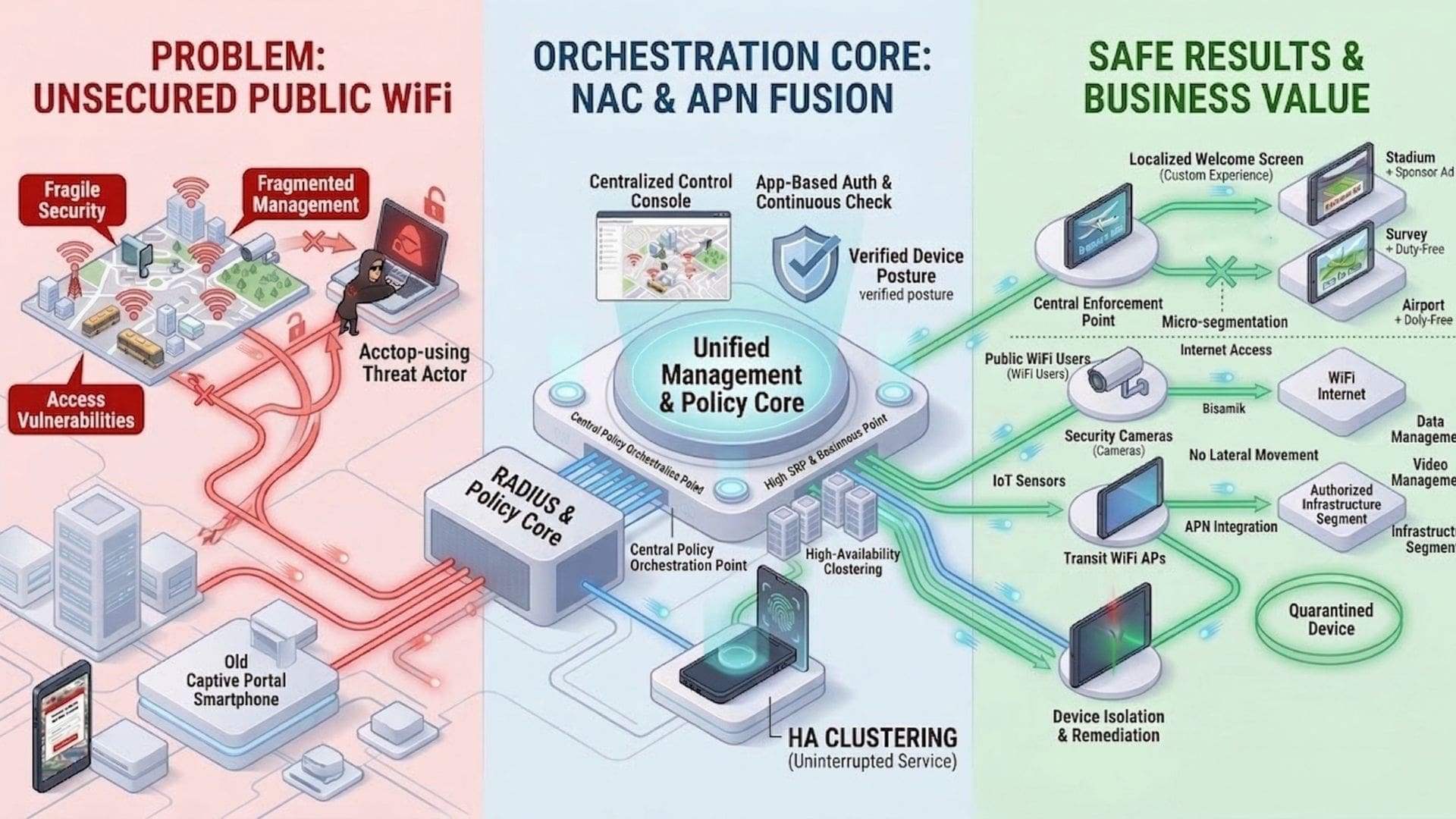
Public WiFi Security operates through a centralized control layer integrating NAC and APN technologies.
All users, devices, and infrastructure components are continuously authenticated and dynamically segmented.
Policies are enforced in real time to ensure secure connectivity, visibility, and control across distributed network environments.